Fake Mobile Apps Impersonate and Infiltrate
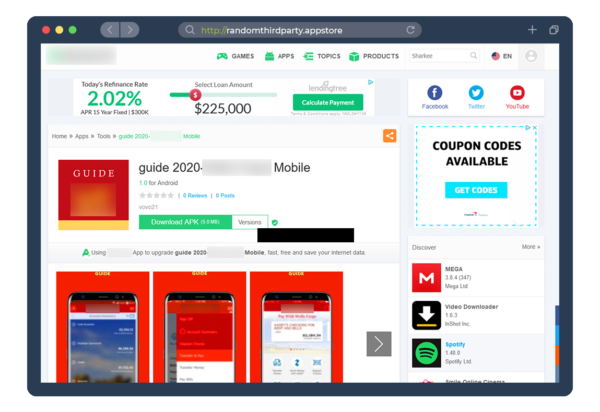
A fake mobile app hosted on a 3rd party store
Fake mobile apps impersonate trusted brands and compromise mobile devices with malware designed to steal confidential data. By replicating the appearance and functionality of legitimate apps, they trick unsuspecting users into installing and interacting with malicious content. This can result in fraud losses, mistrust, and brand damage for organizations.
PhishLabs protects your customers and brand value by detecting, analyzing, and relentlessly pursuing the takedown of fake mobile apps undermining your organization.
Prevent Brand Abuse from Cloned Apps
Prevent Brand Abuse from Cloned Apps
As consumers rely on mobile apps to socialize, conduct business, and make financial transactions more frequently, bad actors are creating fake and unethical apps to engage with unassuming users. Cloned apps – identical copies of legitimate apps – are widely available in official and unofficial app stores, often lack security updates, and have high potential for compromise.
Cybercriminals impersonate legitimate brands using official company logos, trademarks, and images to convince a user to download and install a cloned app. Preying on the sense of security associated with a trusted brand, they steal credentials and intercept SMS authentication codes.
PhishLabs protects your brand by finding and removing unauthorized clones and out-of-date versions of your mobile app. We actively monitor hundreds of official and unofficial app stores to detect references to your brand, validate the findings, then quickly mitigate abuse on your behalf.

Reduce Mobile Banking Trojan Fraud

Mobile apps have become an essential tool to perform basic tasks in the modern world. Threat actors are aware of the opportunity this creates and use malicious apps to commit fraud. Banking Trojans are easy to implement, difficult to detect, and appear harmless in the form of a game or common business app.
Triggered when a legitimate banking app is launched, Trojans present the user with an overlay that replicates the real login screen. When the user enters credentials, the malware steals data and removes the overlay, transitioning back to the legitimate banking app so not to alert to the compromise.
With PhishLabs, organizations can reduce the risk of credential theft from mobile banking Trojans. We analyze mobile malware samples and related infrastructure to gather high-value threat intelligence that organizations can use to improve authentication and prevent fraud.