Threat actors are increasingly registering new domains to launch malicious campaigns against enterprises. Identifying suspicious domains, as well as monitoring existing ones for changes, is an overwhelming and reactive task for many organizations. In order to minimize the risk spoofed domains pose, security teams must be able to efficiently detect abuse and understand what is required to mitigate threats.
Using a fraudulent domain to conduct a cyber attack is an optimal choice for threat actors because a domain string can be manipulated an endless number of ways. A spoofed domain can be used to host malicious or unauthorized content, lead to a phishing site, or redirect to an unintended page.
The consequences of a spoofed domain can be damaging for an organization and result in everything from loss of brand trust to data compromise.
Below are a few examples that demonstrate how domains can be used to harm an organization.
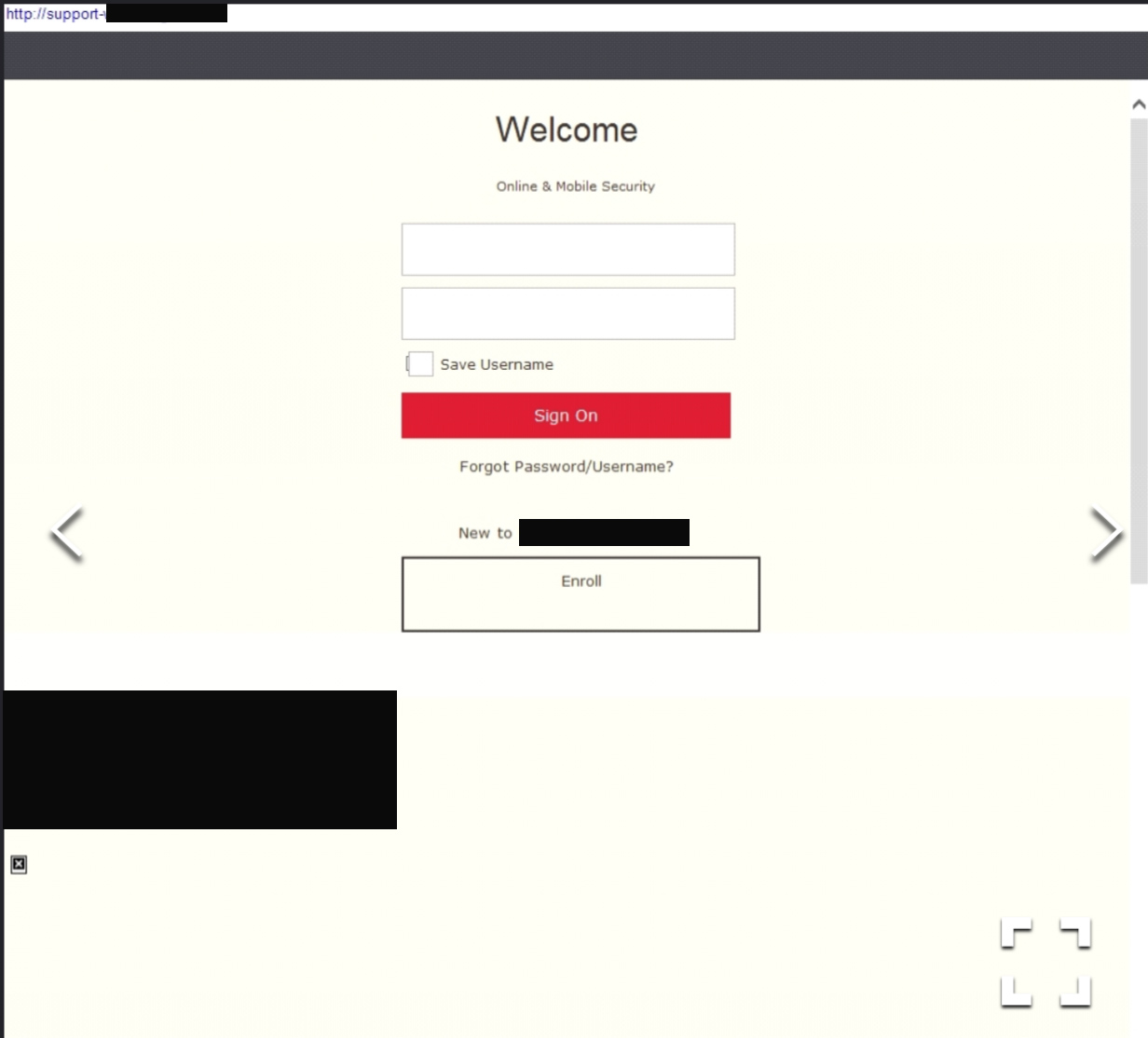
In the first example, the domain name impersonates technical support for a large enterprise to execute a credential theft scam. After this page was identified as malicious it was promptly taken offline.
Domain: http://support-{redacted}-{redacted}.com
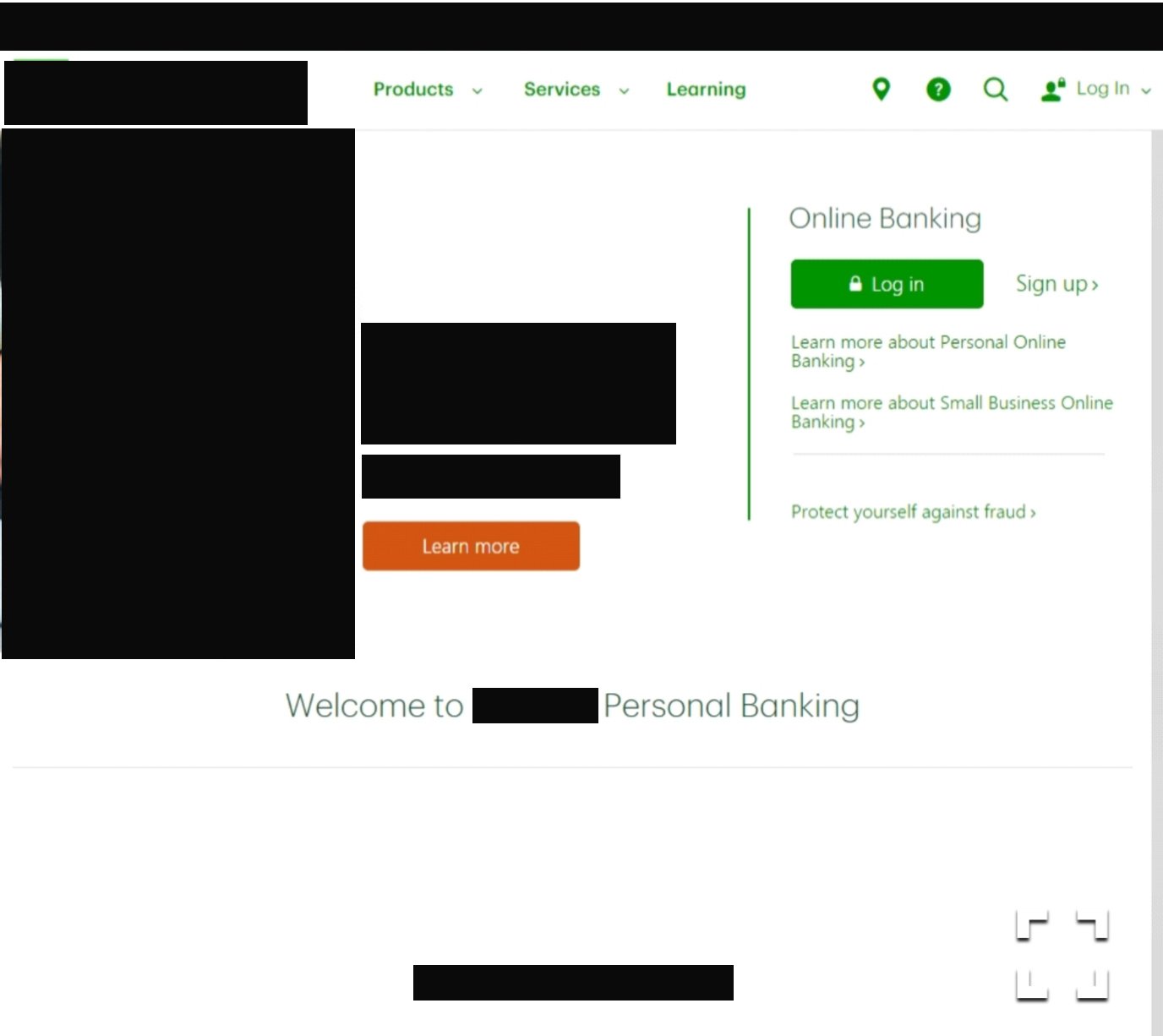
The second example uses typo-squatting to resemble a large financial institution. The domain has a live mail exchanger (MX) record, giving the threat actor the capability to conduct malicious email campaigns.
The variety of ways a domain can be manipulated as well as the ease of which a domain can be registered make abuse of the domain system compelling for threat actors. Last year alone, PhishLabs observed a year-over-year increase in the use of free domains to host phishing sites, making up 32.6% of the volume. Enterprises can effectively manage spoofed domains by implementing a mature and ongoing process for collection and curation. Once a domain has been established as a threat, security teams must have a comprehensive mitigation strategy that includes taking the threat down as well as using indicators to prevent internal users from accessing it.