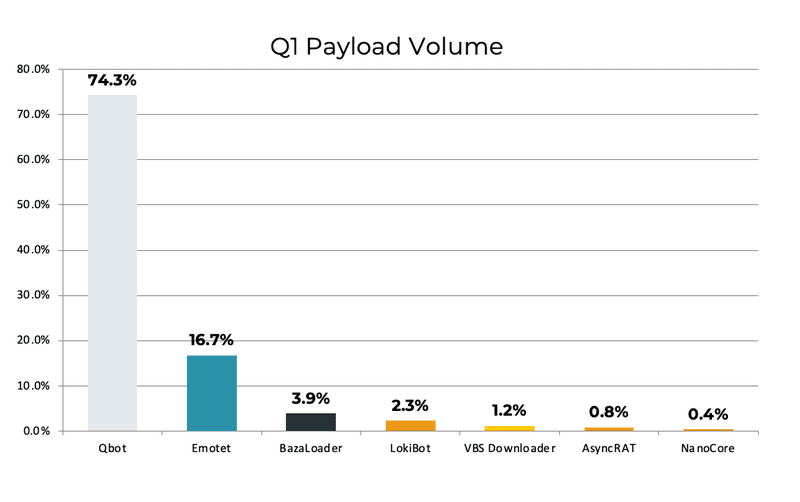
Qbot payloads targeting enterprises contributed to almost three quarters of all email-based malware since the beginning of 2022. Although reported malware activity among families continues to fluctuate dramatically from quarter to quarter, QBot reports in Q1 represent the highest volume of a single malware variety over the past 12 months.
Phishing lures delivering payloads remain the primary delivery method of ransomware. PhishLabs monitors payload families reported in corporate inboxes to proactively prevent and remediate these threats. Below, we highlight the top payload threats targeting enterprises in Q1.
Qbot
Qbot payloads contributed to 74.32% of all malware reports in Q1, representing the largest volume of email-based malware. QBot has consistently stood among the top payloads targeting organizations, and is connected with REvil, Egregor, ProLock, and MegaCortex ransomware families.
QBot is a modular banking trojan most often distributed via phishing emails that contain malicious attachments such as excel documents or fake invoices. Recently, QBot has been documented in attack campaigns that feature rapid movement from initial infection to data exfiltration. These tactics were previously seen in Fall of 2021, and demonstrate the collection and extraction of browser data and Outlook emails within a 30 minute window.
Emotet
Following its dramatic takedown in January 2021, former leading payload Emotet reemerged in November. Since its detection, reports of Emotet have grown considerably, representing nearly 17% of reported payloads in Q1.
Emotet was originally developed as a banking trojan and often works in tandem with TrickBot and Ryuk ransomware. Before its operations were temporarily dismantled, Emotet was considered the most dominant modular botnet, commanding more than 1.5 million machines at its peak. VM-aware and polymorphic, Emotet is traditionally delivered via phishing emails and is known for using novel attack methods such as email hijacking. Emotet operators are also considered very skilled at evasion.
BazaLoader
BazaLoader was the third-most reported payload in Q1, contributing to just under 4% of attacks. Despite an almost nonexistent showing in Q4, quarterly reports have documented BazaLoader as the top payload twice, keeping true to the unpredictable nature of malware activity.
BazaLoader is a backdoor/loader trojan often distributed in multi-stage phishing campaigns. This includes hybrid vishing attacks where both misleading emails and fake call centers are used to engage with victims and ultimately infect their devices.
BazaLoader is often used to deploy Conti and Ryuk ransomware. Its developers are believed to also be responsible for Trickbot malware.
Noticeably absent from the top reported payload families in Q1 were reports of ZLoader. In 2021, and as recently as the beginning of January 2022, ZLoader was responsible for multiple high-volume campaigns. ZLoader is a banking trojan and popular malware-as-a-service (MaaS) with ties to Egregor and Ryuk ransomware strains.
A record number of organizations reported being impacted by ransomware last year, with email phishing facilitating the majority of attacks. In order to prevent the delivery of malicious payloads, security teams should prioritize the proactive detection, analysis, and removal of suspicious emails.
