In Q1, more than 51% of phishing sites abused paid services, according to the Agari and PhishLabs Quarterly Threat Trends & Intelligence Report. This is the first time in five consecutive quarters where the majority of phishing sites were staged using Paid Domain Registrations or Compromised Sites. Phishing volume as a whole continues to increase in 2022 in comparison to the same time period last year, and continued analysis of how these sites are staged aids in the intelligence collection and early detection of threats.
Every quarter, Agari and PhishLabs analyze hundreds of thousands of phishing and social media attacks targeting enterprises, their brands, and their employees. In this post, we analyze phishing activity targeting organizations, their brands, and customers.
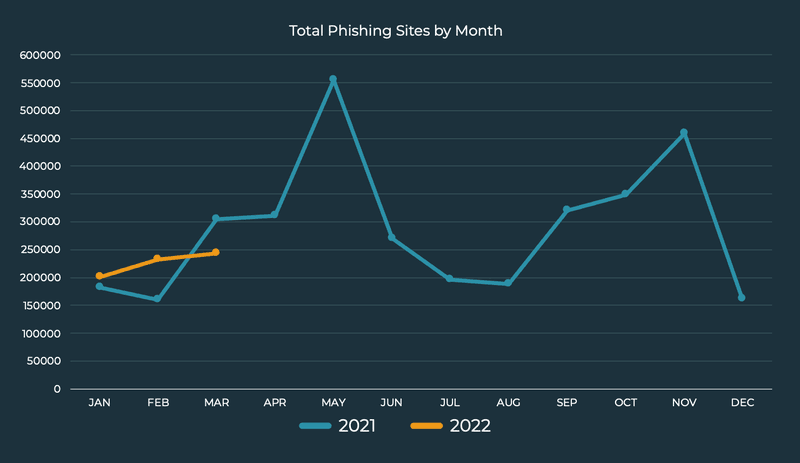
The volume of malicious phishing sites have increased 4.4% from Q1 2021 to Q1 2022. Month-to-month activity in 2022 has so far lacked the volatile behavior associated with 2021, increasing in a steady and somewhat predictable manner. Looking ahead, we anticipate spikes in activity will occur, as opportunistic actors target vulnerable brands and businesses.
Industries Targeted
In Q1, the Financial Industry was targeted most by credential theft phish, despite experiencing a decline in share of 7.4% from Q4. Financials have been heavily targeted for four consecutive quarters, and represented 53% of total phishing attack volume in Q1.
The technology sector as a whole experienced an increase in attacks in Q1. Social Media organizations led the group, experiencing a 9.6% increase in attack volume and representing 21.5% of credential theft phish. Webmail/Online Services, E-commerce, and Cloud Storage/Hosting also represented the top targeted industries in the technology sector, contributing to 5.5%, 1.9%, and 1.7% of attack volume. All three industries experienced an increase in share in Q1.
Telecoms were the only industry to experience a decline in Q1, dropping 10.3% in share from Q4 and contributing to 14.3% of observed phishing attacks.
Methods of Staging Phishing Sites
In Q1, 51.8% of phishing sites abused a compromised webpage or were staged using a paid domain. Abuse of paid services steadily increased each quarter throughout 2021, and ultimately reached the milestone after a 3.2% increase in Paid Domain Registrations in Q4. Compromising existing websites has consistently remained the top method to stand up credential theft phishing sites, representing 35.1% of share of all incidents in Q1.
Free Services and Tools were used to stage phishing sites 48% of the time. Free Hosting was abused most, representing 18.3% and experiencing the only increase in share within the group.
Tunneling Services declined slightly and represented the second spot, experiencing 15.1% of abuse. URL Shorteners and Free Domain Registrations also experienced a decrease in volume, representing 7.1% and 6.4% of staging abuse volume, respectively.
Top-Level Domain Abuse
Four Legacy Generic Top-Level Domains (gTLDs) contributed to nearly 66% of all phishing sites in Q1. This represents a 9.1% increase in abuse from Q4. Legacy gTLD .com experienced a nominal decrease in share, however still represented nearly half of all phishing activity. Legacy gTLD .org experienced the greatest increase in share of abuse among gTLD’s, accounting for 11.5% of all phishing sites staged.
Country Code Top-Level Domains (ccTLDs) were abused less in Q1, declining 15.5% in share from Q4. Notably, ccTLD .ca, the second most abused domain in Q4, completely dropped from the top ten in Q1. Only three ccTLDs made the top ten list in Q1.
Phishing continues to be the most significant threat to enterprises, employees, and their customers. Despite this, the balancing out of phishing volume confirms actors are increasingly targeting victims through a broad array of unconventional channels and platforms. To effectively detect threats targeting organizations, security teams require comprehensive visibility into relevant online environments.
