A threatening social media post targeting an executive, employee, brand, or any other asset often has merit to it, and investigating the online accounts associated with the threat actor is imperative in the process of assessing risk. By mapping social media accounts operated by the threat actor, as well as general social media risk monitoring, you can build a more comprehensive profile of the user and better assess the risk posed. It can also reveal the real-life identity of the user if they have attempted to remain anonymous.
We recently published a blog focused on the importance of determining a social media user's location, and the same is true in gauging the behavior of an online user through posted content across their social media accounts. Past activity, interactions, and anonymous accounts may all help to determine the level of risk and can provide security teams valuable insight into whether or not mitigation should be pursued.
As with any OSINT investigation, it's important to ask yourself the right questions. A good one to start with is “Why?" This will allow for the exploration of the threat actor's motivations, which is valuable context for threat assessment. Questions can include:
- Is there evidence of them claiming to be wronged by the asset which may have provoked the posted threat?
- Was this post the only mention of this asset, or is there a history within their post activity that contains other mentions of it?
- How familiar are they with this asset?
- Is it within their posting nature to publish threatening content made toward other targets, or is this an outlier among harmless posts?
- Does their post history present evidence of extreme opinions?
- Are they engaging with other users who post similar content in support of the target user's ideologies?
Take the example below of a user posting a threatening statement towards a large corporation's CEO, John Doe (revised and redacted).
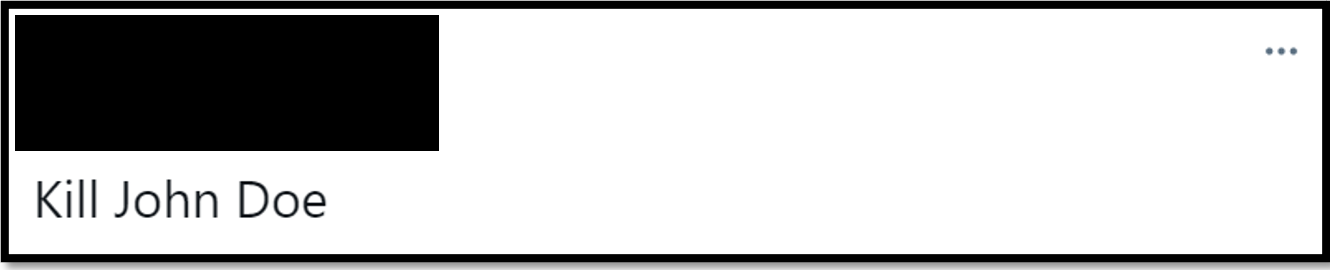
Analyzing the post history of the threat actor's known account on the known platform is a good start in determining risk levels. Sometimes, this will provide all of the information needed to accurately assess risk. In this case, it did not. However, it did suggest the user may hold extreme views.
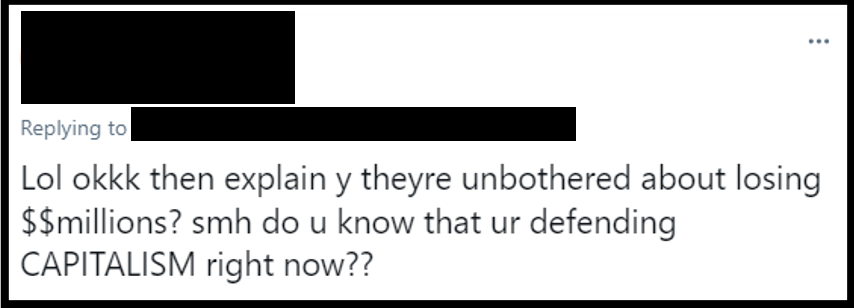
While this information is inconclusive on its own, it does show that further investigation is warranted. The next step is to identify and analyze other social media accounts operated by the same actor. This can provide additional findings that support a high confidence assessment of risk.
Finding additional social accounts can range in difficulty. If the threat actor doesn't provide links to their other profiles within their About sections or posts, it requires precise attention to detail to find the needles in the haystack.
One method of discovering their accounts on other platforms is to perform specific keyword searches within their posts. For example, if you're trying to find an account linked to a user that is on a different platform, a good starting point is to simply search for the secondary platform's name (and its common variations) within the original profile. This can yield false positives but can also provide the user's secondary profile if they linked it. At the very least it will indicate if they may own an account on the platform.
Some users may also share uploaded screenshots of posts from other platforms or forums which could provide a lead to pivot your investigation to that network. This was the case in the example investigation above. The user posted a screenshot of deleting an account on another platform. From this, we know that:
- They had a profile in the past, where evidence may still be present
- They're likely no longer using the platform
Examining unique usernames across other platforms is another useful method of mapping accounts that belong to the same threat actor. Cross-analyzing posts and interactions with users on the newly discovered account can build confidence levels of the accounts being operated by the same user. Alternatively, the reverse discovery may occur. The newly-discovered account can provide evidence of being directly linked to the initially known profile of the threat actor.
The below is a post by an anonymous Twitter user that is liked by the known profile of the threat actor. If we can conclude both profiles belong to the same individual, post activity linked to these accounts can provide valuable insight into the threat actor's motives.
Sometimes, threat actors will use an anonymous or burner account to target assets in parallel to operating their primary account. The possibility of these accounts being connected should be explored either through mentions, within the following/follower lists, and with mutual connections, etc. Post history and interactions on any linked accounts should then be analyzed as a part of your risk assessment.
In conclusion, investigating a social media threat actor's account and discovering their other profiles can be instrumental when determining the risk of a potential threat. Mapping out accounts operated by the actor can lead to findings and context that substantially change the risk assessment. The evidence collected can also aid in mitigation efforts for high risk threats that are targeting specific individuals, brands, and other assets. In addition to these actions, a strong social media protection solution will also aid in identifying and minimizing risk.
Learn about how PhishLabs can help:
