Cybercriminals routinely exploit unsuspecting employees and other participants in business ecosystems, like third-party vendors, with increasingly complex cyber threats. Without cyber security awareness based on real-world threats, enterprises are more vulnerable to email-borne attacks that can negatively impact a business’ operations, growth, and bottom line.
Regardless of how sophisticated your technical cybersecurity stack is, your end users are the key to ensuring strong data protection and risk reduction. However, many lack access to:
- Engaging, interactive security awareness training
- A clear understanding of risky or suspicious threat scenarios
- An easy way to report potentially malicious activity
Add to that a lack of time, budget, and know-how, and it’s no wonder that 95% of data breaches are the result of human error. To build threat resilience, organizations need an effective, easy-to-use solution that boosts end user cyber threat knowledge without impacting daily productivity.
Fortra’s Terranova Security is an award-winning security awareness training provider, delivering targeted, engaging training with a practical, people-centric approach. Each learning module and phishing simulation template is designed to reduce risk and help create a strong human line of defense against cyberattacks.
PhishLabs and Terranova Security are both part of Fortra’s cybersecurity portfolio. By providing superior security awareness training to clients worldwide, Terranova Security is strengthening Digital Risk Protection strategies for global enterprises.
Strengthen the Human Firewall
Backed by dedicated a dedicated Customer Success team, Terranova Security makes it easy to build risk-based campaigns that feature the industry’s highest-quality training content and real-world phishing simulations.
Once implemented, you can empower any employee to understand warning signs related to cyber threats like phishing, social engineering, data privacy, compliance, and more. Terranova’s Security Awareness Training is engineered to ensure continuous behavior improvement for all participating end users.
Risk-Based Awareness Training to Avoid Data Breaches
With Terranova’s Security Awareness Training, you can:
Terranova’s Security Awareness Training modules are also mobile responsive, which means employees can complete courses on the go. As a collaborative partner, you can leverage years of experience and subject matter expertise to help plan and execute a security awareness program focused on the threats your employees encounter every day.
Real-World Training Scenarios that Drive Positive Behavior Change
To give employees and third-party vendors the hands-on experience they need to consistently identify cyber attack red flags and report suspicious activity, you need real-world phishing simulations. Ones built on templates that reflect common threats end users may encounter in their day-to-day. By exposing them to simulated email or other attacks, intermixed with daily communication, they’ll be better positioned to change unsafe behaviors over time.
In addition to customizable phishing simulation templates, Terranova’s Security Awareness Training enables you to build personalized campaigns centered around different topics. Campaigns include various module types, such as:
- Microlearning and nanolearnings
- Immersive, informative Cyber Games
- Just-in-time reinforcement training for clickers
- Pre-configured digital communication tools
Supported by a proven 5-step framework, the Terranova Security solution keeps your training program aligned with your objectives from the start, with campaigns that are easily managed and automated in the Security Awareness Platform. Clients love the diverse content library that’s backed by respected industry experts and continually updated to ensure training is always easy to understand and up to date.
Strengthen Your First Line of Defense
Even the most robust email security technology can’t filter 100% of phishing emails out of employee inboxes. This leaves businesses susceptible to devastating attacks, and humans to recognize, report, and act on suspicious activity.
Security Awareness Training from Terranova Security drives continuous, improved security awareness designed to change unsafe online behaviors, reduce the human risk factor, and counter a wide variety of cyber threats targeting enterprises and their employees. Put users first with targeted, engaging training approach that reduces risk and contributes to a complete Digital Risk Protection strategy.
Ensure Threat Prevention with Complete Inbox Protection
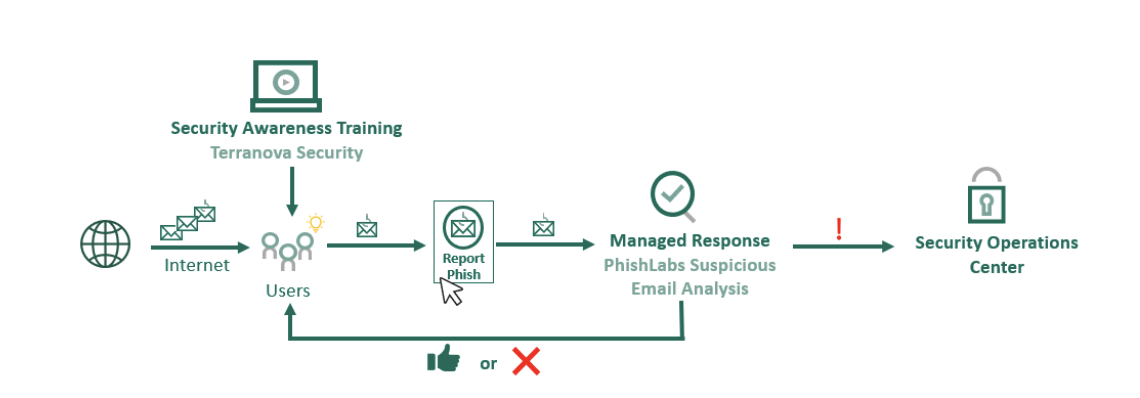
Fortra's Training & Response bundle employs both Terranova Security Awareness Training and Suspicious Email Analysis to ensure that advanced email threats are identified, easily reported, and quickly mitigated, in turn reducing workload on your SOC, enhancing the accuracy of threat detection, and featuring a fast and responsive feedback loop.
