In Q3, nearly 80% of threat actors opted to compromise existing websites or abuse free tools when staging phishing sites, according to the latest data from Fortra’s PhishLabs. While Compromised Sites represented the lion’s share of staging activity, URL Shorteners, Free Domain Registrations, and Developer Tools all experienced increased abuse in Q3 and pointed to sustained criminal interest in no-cost investments to build malicious infrastructures.
Every quarter, Agari and PhishLabs examine hundreds of thousands of phishing and social media attacks targeting enterprises, their brands, and their employees. In this post, we analyze phishing activity targeting organizations, their brands, and customers.
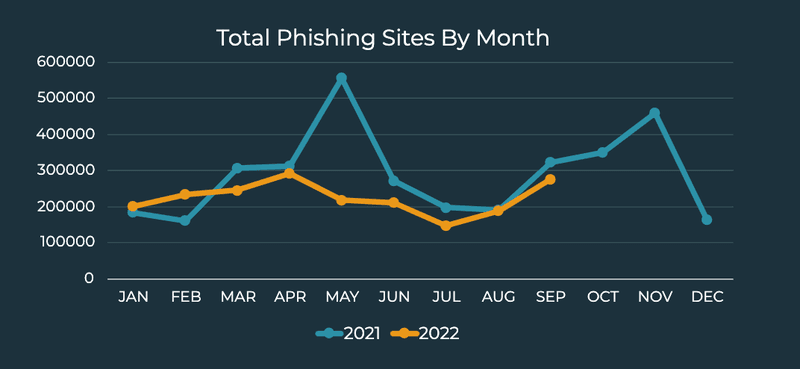
In Q3, phishing volume increased month-over-month, with the second highest activity for the year occurring in September. Phishing volume for the quarter behaved similarly to the same time period last year, with a dip in the summer before increasing in the fall. Overall activity was down 15.26% from Q2 2022, however phishing count is trending up as the end of the year approaches.
Top Industries Targeted
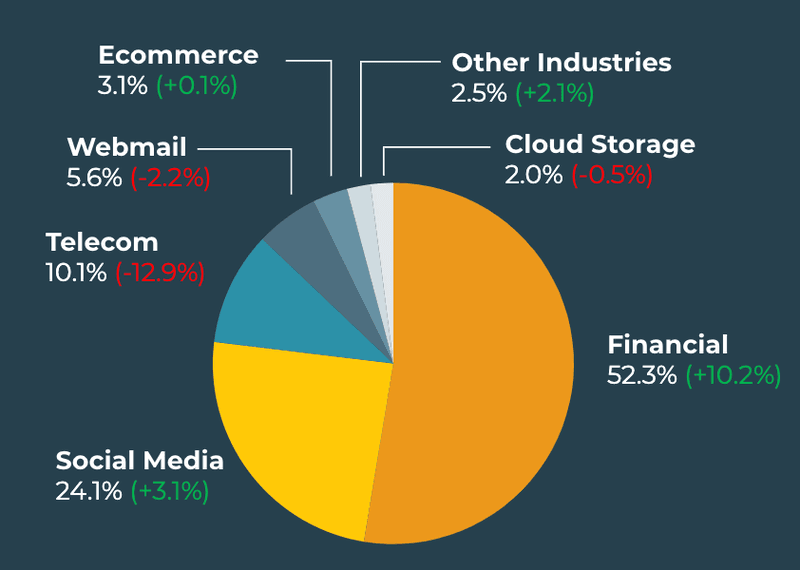
Financial Institutions were the most impersonated industry in Q3, accounting for 52.3% of phishing site volume. This demonstrates a more than 10% increase over Q2 and was the largest jump in activity among all industries. Finance consistently experiences the majority of credential theft attacks.
Social Media accounted for nearly a quarter of attack volume in Q3, overcoming former second place Telecoms. While Social Media did experience a nominal 3.1% increase in activity, phishing sites impersonating Telecoms declined nearly 13% to represent only 10.1% of overall attacks. This was the largest decline in activity among all industries in Q3.
Attacks on Webmail, Ecommerce, and Cloud Storage amounted to just under 11% of total share in Q3. Both Webmail (5.6%) and Cloud Storage (2.0%) were impersonated less than in Q2, 2.2% and 0.5%, respectively. Ecommerce increased 0.1%, contributing to 3.1% of phishing activity.
Methods of Staging Phishing Sites
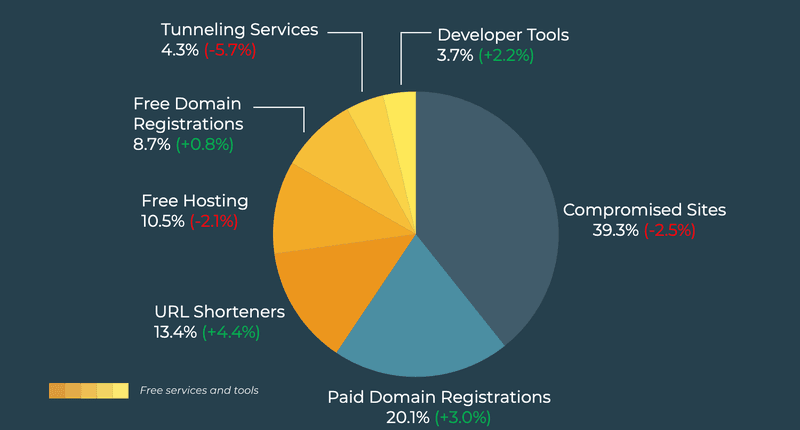
In Q3, 79.9% of phishing sites were staged by compromising an existing website or abusing free services and tools. Compromised Sites were the top method for staging phishing infrastructures, contributing to 39.3% of share of volume. While Compromised Sites decreased from Q2, the group is consistently the top preferred method for threat actors staging attacks.
The abuse of Paid Domain Registrations by criminals has so far increased quarter-over-quarter in 2022. In Q3, Paid Domain Registrations were used to stage phishing attacks 20.1% of the time, increasing 3% over Q2.
Free Tools and Services represented just over 40% of staging methods, with URL Shorteners leading the group. Threat actor abuse of URL Shorteners increased 4.4% in Q3, contributing to 13.4% of share and more than doubling in volume since the beginning of the year.
Free Domain Registrations and Developer Tools also experienced increased abuse, accounting for 8.7% and 3.7% of share, respectively.
Free Hosting (10.5%) and Tunneling Services (4.3%) both decreased in Q3.
Top-Level Domain Abuse
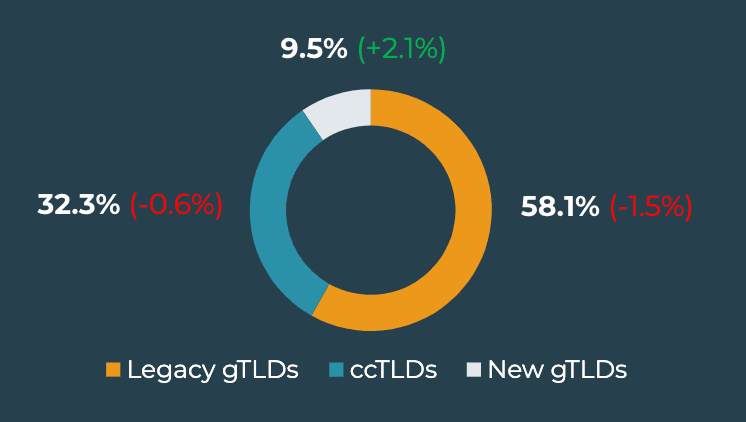
Legacy Generic Top-Level Domains (gTLDs) were used to stage 58.1% of all phishing sites in Q3. While Legacy gTLDs consistently experience the most abuse among top-level domains, this is the second consecutive quarter the category has declined in share.
Legacy gTLD .com was the top offending domain in Q3, contributing to more than 48% of volume. This represents an increase of 1.5% over Q2. Legacy gTLDs .org and .net represented the second and fourth spots overall with each experiencing a decline in abuse.
Country-Code Top-Level Domain (ccTLD) activity decreased in Q3, accounting for 32.3% of share of total volume. The ccTLD experiencing the most abuse was .mx, a newcomer to the top ten and representing the third spot among all TLDs.
While the share of New gTLDs as a whole increased more than 2%, no single domain within the category made it to the top ten. New gTLDs accounted for 9.5% of Top-Level Domain abuse volume.
Phishing activity is trending up as businesses approach the end of the year. While Q3 activity displayed a decline in attack volume from Q2, much of 2022 activity has mirrored the same pattern as last year. Organizations should actively prioritize the detection of malicious sites and the components criminals use to support their infrastructures by continuously monitoring suspicious activity targeting their brands. Additionally, security teams should develop relationships with providers that will enhance the swift and immediate remediation of these threats.
Learn more about how Fortra’s PhishLabs can help protect against phishing activity targeting your brand here.
