 One way to verify if an email is legitimate is to look at the sender's address, the actual sender's address, not just the sender's name. One tactic cyber criminals employ is using the sender's name to trick the recipients.
One way to verify if an email is legitimate is to look at the sender's address, the actual sender's address, not just the sender's name. One tactic cyber criminals employ is using the sender's name to trick the recipients.
The cyber criminal may use a known acquaintance's name or the name of a legitimate company they are trying to spoof. This sounds sophisticated, but it is easy to catch when you see that the sender's address in the email, allegedly from your boss, actually comes from a random, free email account like [email protected].
However, not all phishing emails come from a fake email account that is trying to impersonate a company or a user. Sometimes these emails actually come from a trusted email account. This method, when a cyber criminal hijacks a trusted mailbox, is called account take-over.
Here is an example:
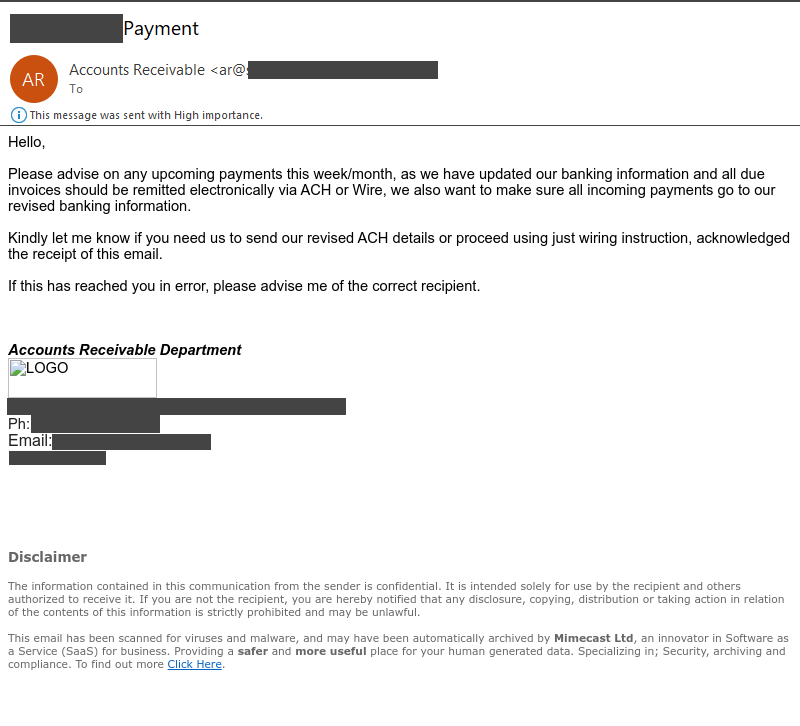
In this example, cyber criminals took over a legitimate account and contacted the company's clients to redirect payments to their account rather than the company's. Since the actual, legitimate email account was taken over, everything about the email was seemingly legitimate, except the request.
Were there red flags? There were, but they were tough to spot.
The typical red flags, such as the sender's address or suspicious links wouldn't help, as everything appeared legitimate. The only red flags were subtle and contextual. There is no email in the “to" field which means everyone was BCCed.
Next, it is clear in the message that the sender doesn't know who should receive the email. They said, “if this has reached you in error, please advise me of the correct recipient." This a sign that the cyber criminal is trying to find the right person) and also asks for an acknowledgement of receipt of the email (an attempt to validate the email accounts they sent the message to.
But these clues are subtle and could be easily missed. In many cases you need to follow your gut. If a request seems out of the norm, reach out to the person outside of that email to verify the request is real.
It doesn't matter if the email appears to be from your CEO or vendor; call, text, message them, or go to their office and ensure they actually sent the email before taking any action or replying. Verification before acting is one of the best ways to protect yourself and your organization from falling victim to this type of attack.