App downloads fueled by COVID-19 lockdowns leapt to 37.5 billion in Q2 of this year, and collective global app usage is surging. Android users' screen time stands out significantly, with an increase of 25% above the weekly average from the previous year. As apps continue to be an integral part of how we conduct business and perform sensitive tasks, bad actors are using fake and unethical apps to engage with unassuming mobile users.
Threat actors know that mobile users are traditionally less suspicious of content on their devices than on their computer, and with increased device use due to social distancing and lockdown restrictions, they are capitalizing on users integrating mobile apps even more into their daily lives.
Brand impersonation is one of the key factors in the success of fake apps. Cloned apps, unauthorized use of logos, trademarks, and images prey on the sense of security that comes with a trusted brand. By creating a fake app that poses as a legitimate one, threat actors increase their chances of convincing a mobile user to install and use the app.
Fake apps can come in many forms. Most prevalent are cloned apps - identical copies of legitimate apps- that can be installed from third party app stores. Cloned apps may lack the security patches that remove vulnerabilities on a device and have the potential to result in a breach. Cyber criminals also spoof apps using an organization's official logo or trademarked content to bombard devices with ads. These ads can run unseen in the background, and are auto-clicked to generate revenue for the threat actor.
Apps can appear to be games or tools but instead deliver trojans to steal data or take control of a device. They also pose as legitimate financial institutions to steal their user's banking credentials. Fake banking apps are so widely available on app stores that the FBI issued a public service announcement warning of their presence.
The examples below show various ways threat actors are abusing mobile apps.
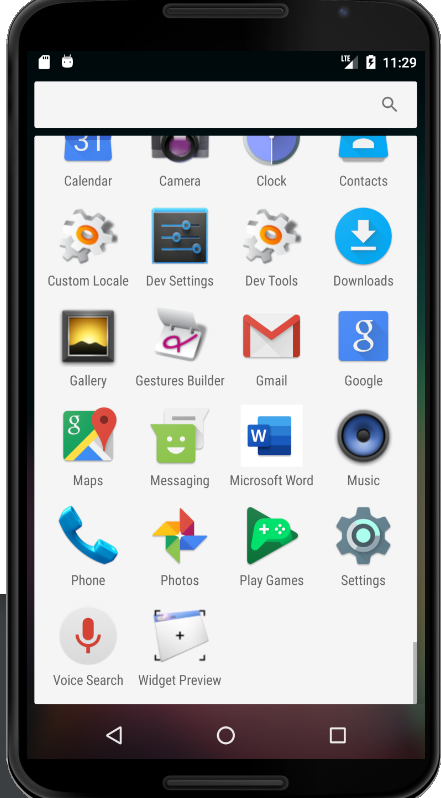
The first malicious app poses as Microsoft Word.
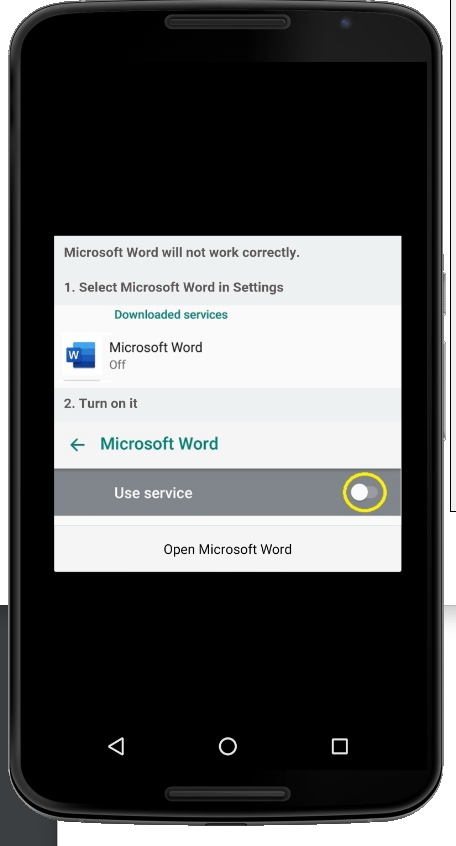
When the app is enabled, it hides Eventbot malware targeting a specific financial app on the device. Once the user opens the targeted app, the malware places an overlay on the screen, and the user unknowingly enters their credentials into the fake login page.
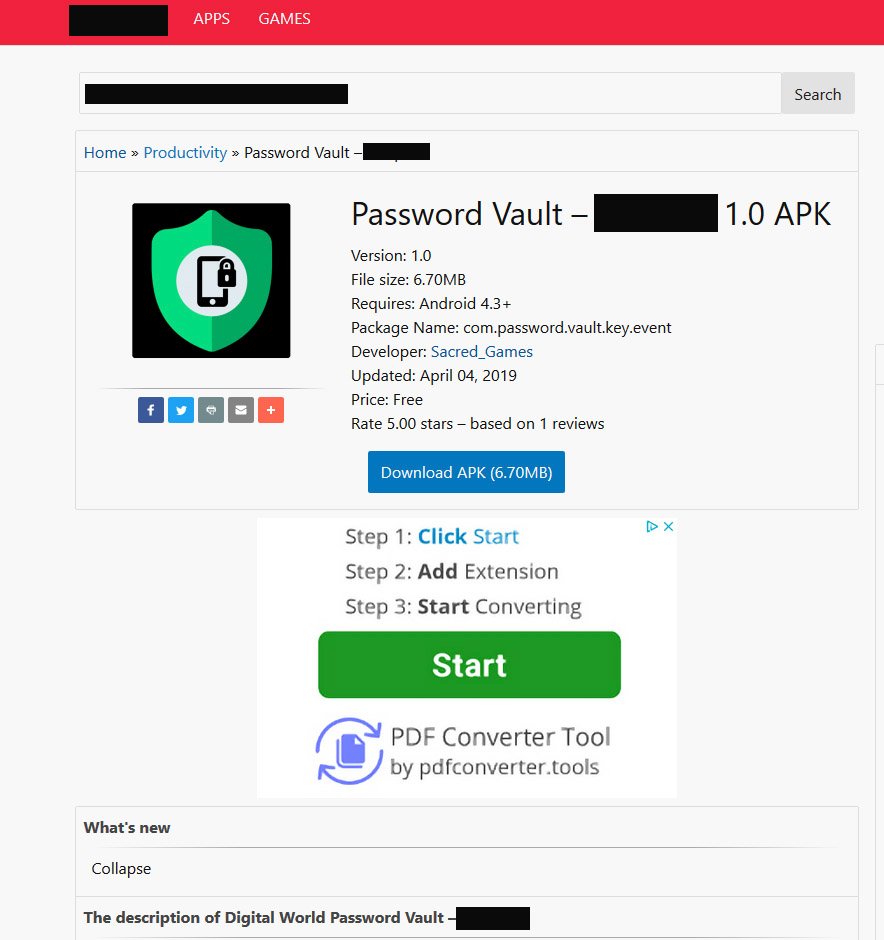
The second example impersonates a secure password manager app. Victims who install and use this app give threat actors direct access to their sensitive information and digital records.
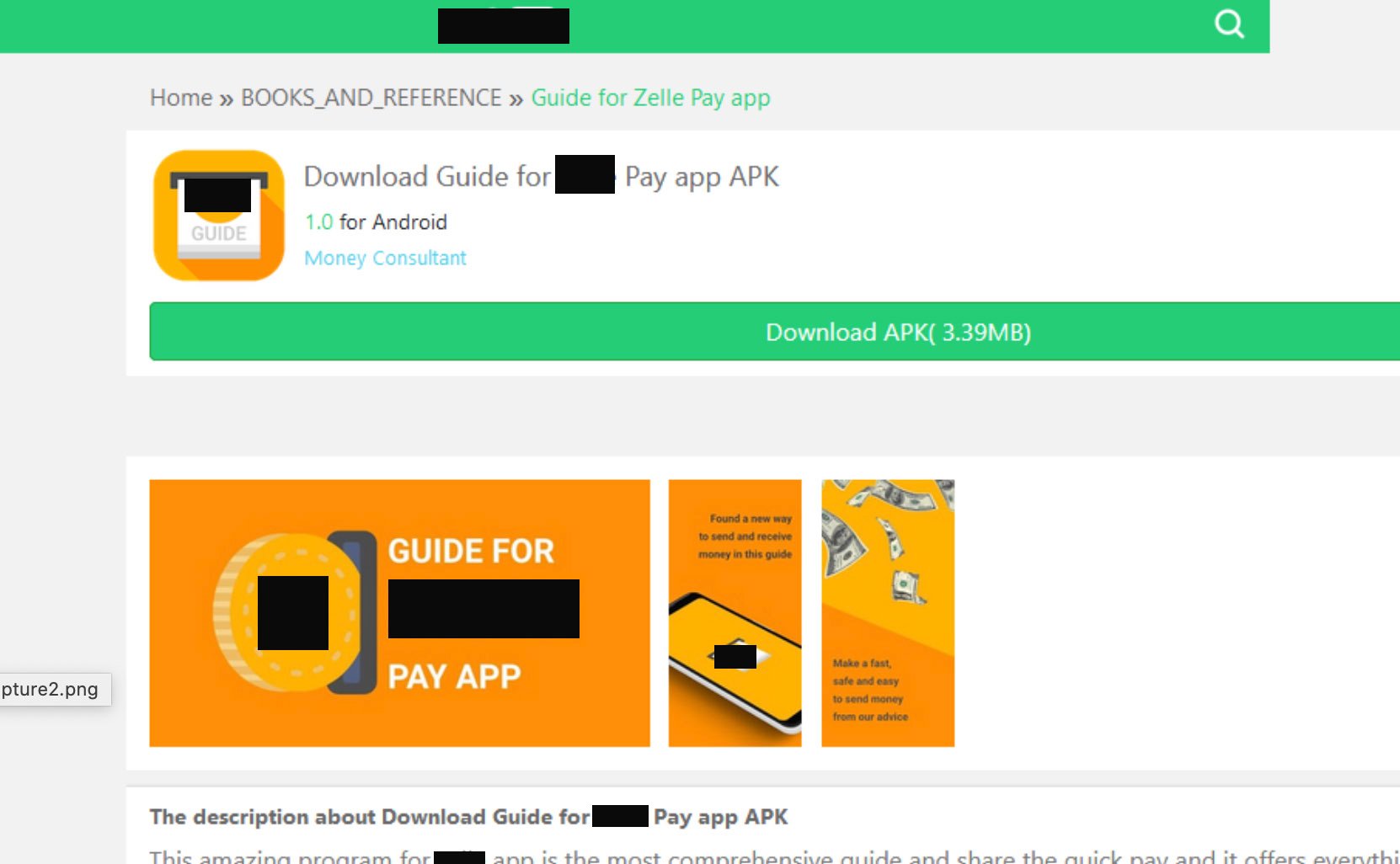
The third example uses a similar logo and images of a popular money transfer app to pose as a guide on how to use their services. Once downloaded, the app serves ads and automatically clicks on them to generate revenue for the threat actor.
As individuals socialize, conduct business, and perform tasks more frequently on mobile devices, the number of apps available to help execute those actions is increasing. Today, Google Play boasts 2.96 million available apps in their store, not to mention the number that can be downloaded from the official Apple App store or hundreds of other third-party stores. Threat actors are aware of the opportunity this creates, and are using fake apps to perform malicious activity, with relatively low suspicion.
Additional Resources:
