By definition, a look-alike domain is a nearly identical, slightly altered domain name, registered with intent to deceive. Cybercriminals register hundreds of thousands of look-alike domains each year with the goal of impersonating legitimate brands and making money, usually by committing fraud. In this post, we'll describe how domains help us communicate on the Internet, the anatomy of a look-alike domain and why we fall for them, how attackers create them, and the best place to begin when facing this common threat.
Domains Are Key to Internet Communication
The Internet was built on one simple principle: communication. Every connected device can be reached using an IP address, and communication happens when information packets are transferred between devices. Technically we are communicating with businesses every day by visiting websites or buying something online. Domain names were originally created to keep up with the explosive growth of the Internet and provide an easy way for people to remember website names. Domains translate to IP addresses so our browsers and email clients can send requests on our behalf to find and communicate with a website or mail server. Similar to a person's name, businesses use domains to establish a unique identity. And similar to using a person's phone number to call them, we can use the numeric IP address to connect to a website. Yet in the same way we don't typically use a friend's phone number to identify them, we don't memorize IP addresses to visit websites.  Thanks to our modern Domain Name System, businesses can send customers to a user friendly website name like www.acmebank.com rather than 65.154.128.12. Attackers know we use domain names to interact with our preferred vendors. They are also aware that we enter credentials to log in to websites, make purchases by inputting credit card details, and exchange emails with these vendors.
Thanks to our modern Domain Name System, businesses can send customers to a user friendly website name like www.acmebank.com rather than 65.154.128.12. Attackers know we use domain names to interact with our preferred vendors. They are also aware that we enter credentials to log in to websites, make purchases by inputting credit card details, and exchange emails with these vendors.
Anatomy of a Look-alike Domain
Domain names act as a map to tell browsers and other applications how to find what we're looking for. Explaining the full structure of domain names and their hierarchy is more complex than this, yet here are the basics: 
- The top-level domain portion on the far right can identify the location where the domain registrant resides, their organizational purpose, or even the industry of the business that registered it.
- The second-level domain section is the address name and unique identifier often manipulated to impersonate domains used for legitimate purposes. They enable our computers to find the server where a website or email is hosted.
- A subdomain is a part of the domain that helps registrants organize a website into different sections or categories. Subdomains can also used to create look-alike domains. Example: phishlabs.000webhost.com.
Using our everyday habits to their advantage, threat actors register look-alike domain names to create confusion. They lead us to believe we are visiting the websites or responding to emails of the brands we trust. Although their uses vary widely, threat actors typically register look-alike domains to profit from a recognizable brand's credibility. Also called a spoofed domain, fake domain, cousin domain, or doppelgänger domain, they typically include a company name, service name, or trademark with a typographical variation.
How Our Brains “Hack" Look-alike Domains
Research shows that look-alike domains “look" legitimate for a reason. The human mind doesn't read the letters of a word. It sees the word as a whole, so our brains quickly recognize words with several spelling errors that, in actuality, look like nonsense. We are always anticipating what we will see next, so our brains are surprisingly good at predicting what will likely appear in the future using context, current inputs, and past experience. If the letters of a word are slightly moved around, we still see the full word in our mind. This principle is called Typoglycemia. It suggests that readers can comprehend text even if there are misplaced letters in the words. Here's an example:
Aoccdrnig to rscheearch at Cmabrigde Uinervtisy, it deosn't mttaer in waht oredr the ltteers in a wrod are. Tihs is bcuseae the huamn mnid deos not raed ervey lteter by istlef, but the wrod as a wlohe.
Reading words instead of letters provides a cognitive shortcut for our brains. We're able to see dominant patterns, batch information together, and conserve mental resources. Since look-alike domains usually have small variations from the original domain, most people don't even notice the difference. Scammers know that anyone reading a look-alike domain containing a slight variation will automatically correct any misspellings, and they use this to their benefit.
Why Do Scammers Register Look-alike Domains?
Threat actors register look-alike domains to impersonate well-known companies, leverage their credibility, and make a profit from various scams. The process is inexpensive, and threat actors will see a large return on their investment if they know what they're doing and move quickly to evade detection.
Creation Techniques
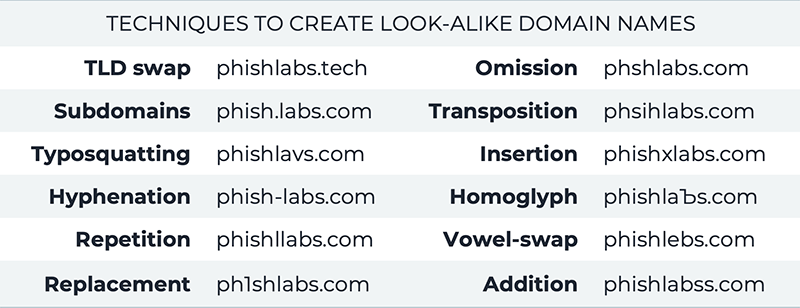
Here are some examples of how attackers create look-alike domain names:
With millions of permutations available, scammers have endless choices when registering a look-alike domain.
The Most Versatile Attacker Tool
Look-alike domains are one of the most versatile tools a threat actor can use to attack an organization because they serve as a foundation for a wide range of cyberthreats. They can host a website on a domain, send email from a domain, or both. Business Email Compromise (BEC), phishing websites, and ransomware attacks are some of the most impactful threats, and they can be relatively straightforward to create. One of the biggest dangers of look-alike domains is that phishing emails such as BEC or ransomware attacks will not be flagged by email security stacks. Since look-alike domains are fully registered and emails with these domains come from legitimate email servers, there is nothing technically unauthorized about them. They will pass through any authentication mechanisms a company has in place, which leads to a high risk of compromise.
Impact to Brand and Reputation
Criminals eagerly use brand impersonation to target prominent organizations online for financial gain. When they register look-alike domains, create poorly designed websites with recognizable logos, and send emails that appear to be legitimate, they diminish the targeted brand's value. Look-alike domains tarnish a business' reputation, too, resulting in customer churn and financial impact. Once they've been duped, customers get angry at both the attacker and the brand. They usually start looking for alternate vendors and tell people they know about their experience.
How Do You Prevent Lookalike Domains?
Sometimes we're asked “where should we start?" when building out a Digital Risk Protection program to manage external threats.
- Create a domain protection program. Domains are a common foundation for many different types of threats. Starting with domains is also easier than creating other external threat programs. If you are looking to protect your organization from brand impersonation and build out a domain protection program, start by collecting new domain data, then put in place a practice of filtering or curating data that leverages technology and people.
- Create your playbooks for mitigation using a combination of domain takedown services and/or IT security controls.
- Continuously monitor new and existing domains. Domain monitoring should be a high priority for any security team. Watching for indicators of brand impersonation such as mail record changes or new infringing content will keep you ahead of the game and possibly lead to disrupting an attacker's infrastructure before it goes live or causes any damage.
To learn more: