Obtaining the location of a social media threat actor can provide important information in the process of assessing risk. Verifying a geographical region of a user is vital in determining the credibility and risk level of the posted threatening content. Investigating true locations of threat actors can evidently turn a seemingly baseless low risk social media threat into something that may be actionable and worthy of escalation through your social media protection program.
Determining the location of a social media threat actor varies in difficulty level. Some users are generous with providing their locations, listing the cities they reside or frequent within their profile's About sections or by geotagging their posts. However, chances are high that a user will not be so willing to share their location if they are posting threatening content in effort of remaining anonymous online.
We also need to consider that a capable threat actor is likely to have anticipated the likelihood of threat hunting and has attempted to deploy countermeasures to frustrate detection. In terms of identifying a location, the user may spoof their geographical region by providing false information within their profile. For example, they could list a false location within their About section and posts as a defensive tactic.
Scrutinize Everything
Deeper examination can be conducted of the threat actor's posts to begin narrowing in on a geographical location of the user. Posts which contain personal images taken by or belonging to the user are a great starting point. Analyzing a picture uploaded by the user in a public setting can provide ideas of where they're located. For example, identifying famous landmarks in the background or even studying a subway ad will offer clues.
Posts may also include pictures taken within the individual's home which can provide evidence of a probable geographical region. This can be something as simple as grocery bags with prints of regional supermarkets on them or analyzing the socket pattern on an electrical outlet seen in the background.
Social media users may also post screenshots of their phones or pictures of their computer screens. By analyzing the date and time stamps displayed on the screens compared to the ones seen within a post, we can likely determine the time zone of the user.
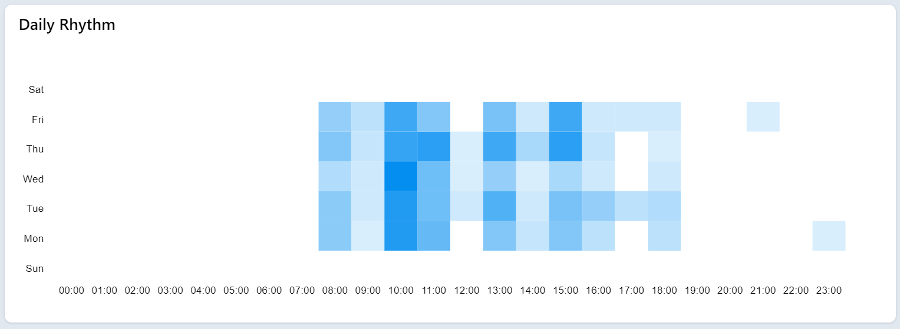
Humans are habitual creatures, and we tend to sleep. Analyzing the pattern of a user's time stamps of published posts as well as the lack of posts within any 24-hour period can also help us better understand where they may be located. This method is most effective in researching a user with a high volume of daily posts. An effective tool which provides insight into a Twitter user's "Daily Rhythm" can be found here: https://accountanalysis.app/.
Using the tool and the PhishLabs Twitter account as an example, we can see when the profile is most and least active. This gives us a general idea of the probable time zone where the user is operating.
Known Associations
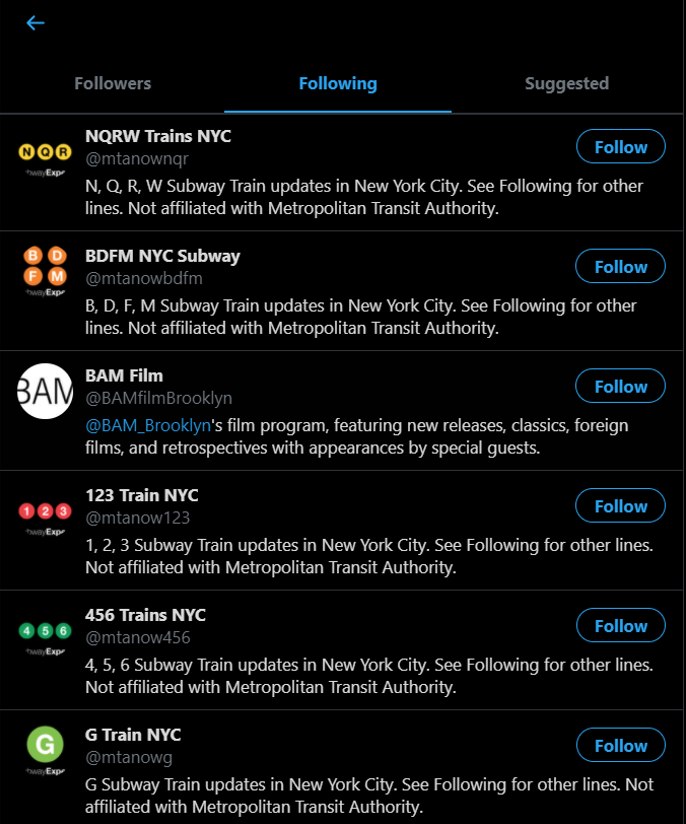
Analyzing posts isn't the only OSINT method of researching a target user's location. Further analysis can be conducted of a user's connections to regionally based accounts. For example, if a user is seen to be following several accounts dedicated to covering New York subway updates, New York restaurants and bars, and New York weather, you can hypothesize that there is a connection between the user and the city.
Below is an example of a threat actor listing their location as Hell, MI within their Twitter biography section which was assumed to be untrue and only used for satire.
Image
Upon further review of their connections, it's seen that several NYC-based accounts for subway updates are being followed by this particular actor. By using identifiers within their timeline and connected accounts, we have valuable information that will help piece together a probable true location.
Researching for a social media user's location can provide key information to security teams. However as the saying goes, “on the internet, nobody knows you're a dog." Just as impersonation accounts exist, users can also impersonate their locations. It's important to practice sound judgement and do your due diligence in coming to conclusions. Where possible, reverse image searching and checking exit data can help provide additional information when investigating uploaded images.
As with any OSINT research, the best tool you can have in your toolbox is curiosity. As you make discoveries within one avenue (i.e. identifying followed regional accounts), you can begin to ask yourself the right questions when analyzing posts and ultimately come to an informed conclusion.
Additional Resources:
