Threat actors are using social media accounts to expose and sell data that has been compromised. While information found on many of these platforms has traditionally been disclosed by enterprises and individuals with intent, cyber criminals are taking information acquired by means of scams and data breaches and promoting their sale on various social platforms not always monitored by security teams. Organizations should put strong social media protection measures into place to avoid this growing risk.
Last month, just under one million sensitive records were exposed in the United States due to breaches. This data is highly coveted by threat actors and can include, but is not limited to, driver's license numbers, social security numbers, passport details, and even access to your bank account. All of this information is considered personally identifiable information (PII) and is the data needed to either act as a link to or identify a particular individual.
Compromised PII can lead to a number of different headaches, and should cyber criminals choose to use that information for malicious purposes, the results could be devastating. Depending on the nature of the data, individuals could find their information used to conduct identity fraud, blackmail, or positioned to conduct fraudulent purchases.
While a great deal of this breached information might find itself as part of a data dump on the dark web or on a paste site, we have seen recent examples of threat actors using social media to make stolen PII public. Although we can only speculate the motivation behind using a previously underutilized social media platform as a means of exposure, it is clear that organizations suffering from data breaches, and the individuals affected by it, should anticipate that their information may now be publicized on platforms traditionally not used in the past.

In the first example, a social media user posts an extensive list of information targeting a single individual, including personal and financial data. Included is the victim's credit card information, home address, and social security number, opening the door to a series of financial fraud opportunities as well as identity theft. The IP address is also compromised, potentially allowing the cyber criminal direct access to the victim's device.
Image
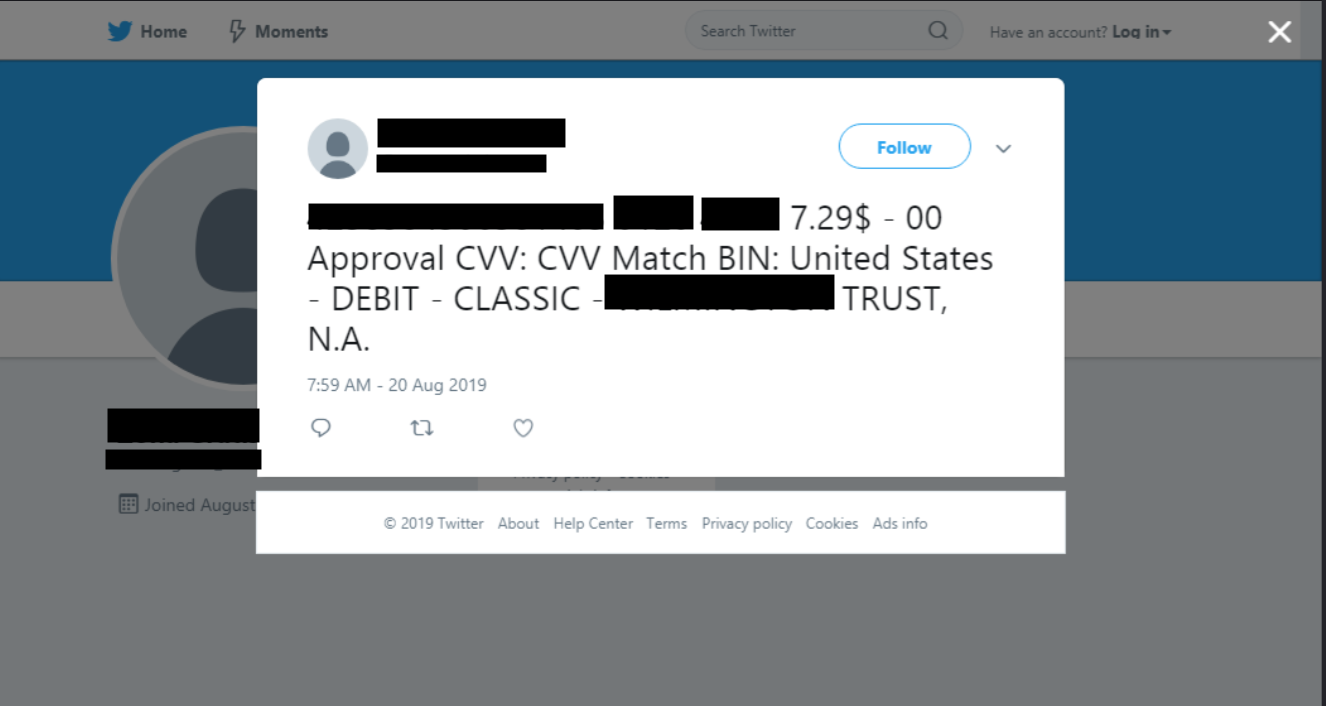
The second example uses Twitter to expose sensitive debit card information associated with a large financial institution. While the Tweet does not publish the account holder's name, it does expose the card number, expiration, and CVV number.
According to Verizon's Data Breach Investigations Report, 86% of today's data breaches that expose sensitive data are financially motivated. That means if PII for your enterprise has been compromised and exposed on any of these channels, there's a good chance it involves a cyber criminal looking to cash in on the stolen information. While the distribution of PII in the examples above still appears to be limited, the presence of leaks on social media indicates that organizations should actively engage in social media threat monitoring and respond to sensitive data leaked by bad actors on these channels.
Additional Resources:
