PhishLabs has identified a Browser-in-the-Browser (BitB) campaign targeting financial institutions with a fake Office 365 (O365) authorization protocol. The attack is delivered via phishing email and redirects the victim to a website impersonating an O365 single sign-on (SSO) page.
A BitB attack is a novel phishing technique that replicates pop-up windows used for SSO in an effort to steal login credentials. The attack uses a combination of HTML and CSS to simulate a fake browser-within-the-browser design that is indistinguishable from a real authorization page. We break down the attack below.
BitB Email Lure
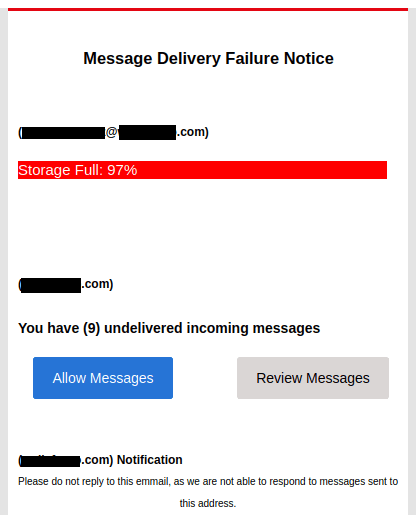
Attackers target the victim with an email phishing lure impersonating a Message Delivery Failure Notice for O365 services. In the lure, the victim is prompted to click on the “Allow Messages” link, which will redirect them to a fake login page.
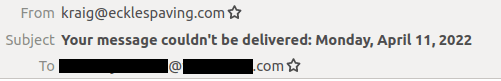
The email is delivered from a third-party address, [email protected].
Within the body of the email, the attacker dissuades the victim from replying directly to the sender, adding pressure to click the “Allow Messages” button. The content also contains a typo, “emmail”.
BitB Webpage
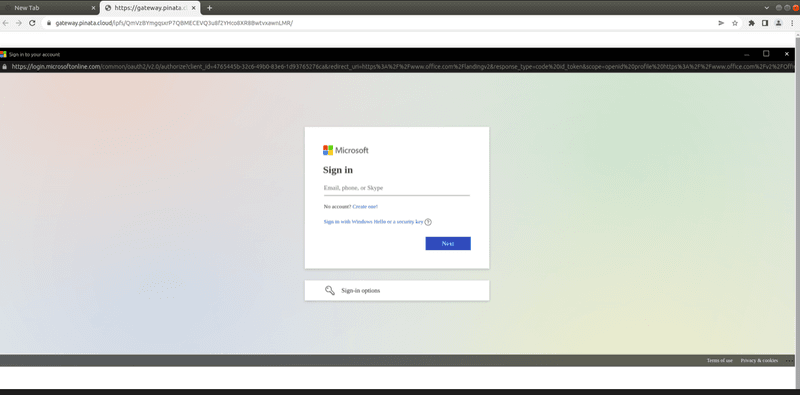
Once the victim clicks the link, they are redirected to a fake login replicating an O365 SSO window where they are prompted to enter their credentials. In reality, the page is an iframe that points to a malicious server hosting a phishing page. Visually, the design is identical to the legitimate page.
The actor is capable of spoofing any legitimate domain, including one with https encryption. URL hovering is ineffective, as Javascript makes it possible to display any URL.
What Makes This Threat Particularly Challenging
Traditional phishing attacks possess two potential points of failure: the phishing lure and the malicious website. If the victim initially falls for the phishing lure, they can still avoid being conned if they spot the red flags on the malicious website.
A website’s URL is one of the key indicators that users can review to gauge legitimacy. After all, the only thing keeping the content of a phishing site from being completely identical to the target site are the creative skills of the threat actor (or the availability of a professionally developed phishing kit.) That’s not the case with URLs, which is why threat actors turn to look-alike domains and similar techniques to make the URL look less “phishy.”
BitB attacks are particularly dangerous because they can present the legitimate URL to the victim on the phishing site. Instead of the URL being a red flag, with BitB attacks it’s a green light. This technique makes it possible for there to be zero visual red flags on the phishing site itself, which means the success of the attack hinges only on whether the victim is fooled by the email lure.
Identification of malicious email lures used in BitB attacks is critical to mitigating these threats. A robust security awareness training program develops multiple layers of habits and behaviors that help employees identify potentially malicious emails and report them to security operations prior to clicking links and being exposed to a BitB phishing site. Solutions that help SOCs analyze and respond to user-reported suspicious emails, such as those provided by Agari and PhishLabs, can identify BitB attacks and mitigate the threat they pose.
PhishLabs will continue to provide updates on these attacks.
