Vishing attacks targeting corporate users have more than doubled for the second consecutive quarter, according to PhishLabs’ Quarterly Threat Trends & Intelligence Report. Response-Based attacks such as these are increasingly targeting corporate users and stand alongside email-based Credential Theft and Malware attacks to make up the top attack vector targeting enterprises.
Every quarter, PhishLabs analyzes hundreds of thousands of phishing and social media attacks targeting brands and their employees. In this post, we take a look at the top threats detected in corporate inboxes that we’ve analyzed and mitigated with our Suspicious Email Analysis solution.
Credential Theft
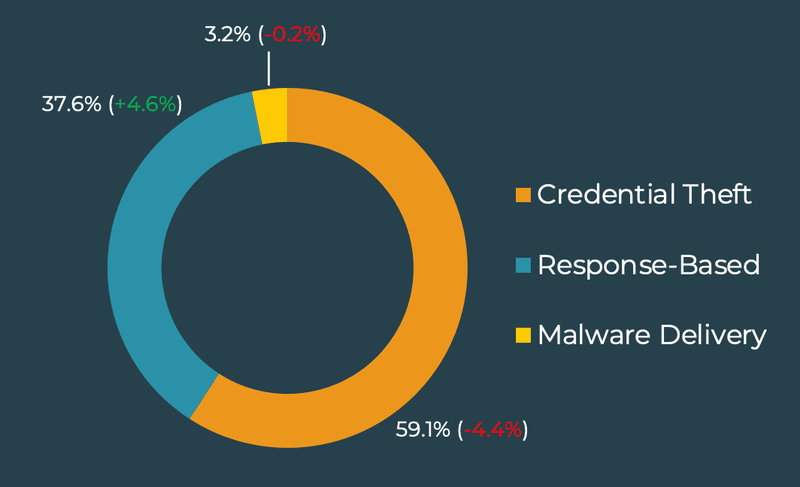
Credential Theft is the most commonly reported email threat to corporate users. Although slightly down this quarter, 59% of all reported emails were Credential Theft attempts. Notably, more than half of these reports are targeting Office 365 accounts. Attacks on O365 have increased in both count and percentage in share for four consecutive quarters, now consisting of 51.6% of all Credential Theft incidents.
O365 credentials, particularly those that exercise Single Sign-On (SSO) hold significant value to threat actors as they may provide access to critical data as well as a broad variety of in-network applications. The continued targeting of these accounts means security teams should prioritize their safety.
Response-Based Threats
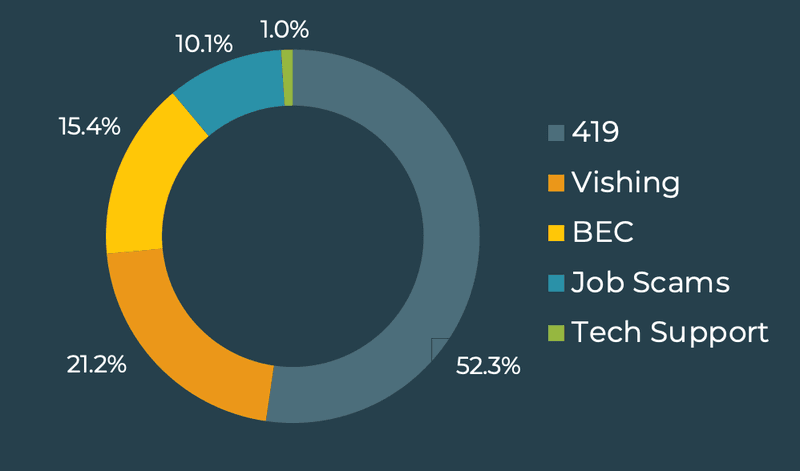
Response-Based attacks are increasing and contribute to just under 40% of threats found in corporate inboxes. Both 419 and Job Scams were reported more often, increasing in share and representing 52.3% and 10.1% of all reports, respectively. The continued growth of Response-Based attacks is a clear indicator that manipulating victims through social engineering is a preferred and effective means of attack.
New Spin on Vishing
Notably, Vishing doubled in volume for the second consecutive quarter, representing 21.2% of all Response-Based threats and overtaking BEC scams as the second most reported threat.
We are seeing a shift away from traditional voice phishing or Vishing, a tactic used to socially engineer victims into disclosing personally identifiable information (PII) or credentials through the use of telephony. Instead, the majority of recent Vishing reports are two-pronged attacks initiated via malicious emails. Unlike traditional Vishing, this approach uses emails crafted to socially engineer victims into taking a secondary step: calling the attacker themselves.
Malware Delivery
Malware is morphing to accommodate new players as the underground threat landscape experiences continued instability. While BazaLoader led payload families in Q3, accounting for 24.7% of reports, the presence of lesser known, one-off payload attacks increased significantly.
Other top payload families of note in Q3 include:
- Agent Tesla (14.3%)
- Dridex (10.4%)
Security teams should expect continued change among malware families and their tools of choice as increased pressure from authorities is causing many to go quiet or rebrand. Additionally, families are expanding operations to include a variety of maliciously-driven affiliates paid to propagate attacks. By broadening the scope of attack functions, threat actors are also making it increasingly difficult for authorities to apprehend responsible parties.
While O365 credentials remain highly coveted by threat actors, the increase in Response-Based attacks and rotation of dominant Malware families indicate criminals are applying their efforts where susceptibilities may be exploited. Enterprises should invest in broad detection and proactive mitigation capabilities to minimize the impact of these threats.
To learn more, access our Quarterly Threat Trends & Intelligence Report.