With more than 2.95 billion people now estimated to use social media, an organization's online presence directly relates to the satisfaction of its customers, as well as its profits. False or misleading images or comments connected with a brand on online platforms can swiftly impact the reputation or even financials of an otherwise successful company.
While most individuals have been taught to identify suspicious or even malicious content presented via email, threat actors know that when it comes to social media that is simply not the case. Criminals that use social media to abuse an organization have broad access to an audience focused on socializing and sharing information, not analyzing Twitter handles or Instagram pages for inaccurate data. These vulnerabilities are appealing to the bad guys and make it easier to convince the victim that the doctored or unauthorized logo they are looking at is in fact, real. That, along with the level of anonymity that social media possesses, allows for an easy and well-distributed scam.
The examples seen below demonstrate how brand impersonation on social media can specifically be a threat to organizations and their customers.
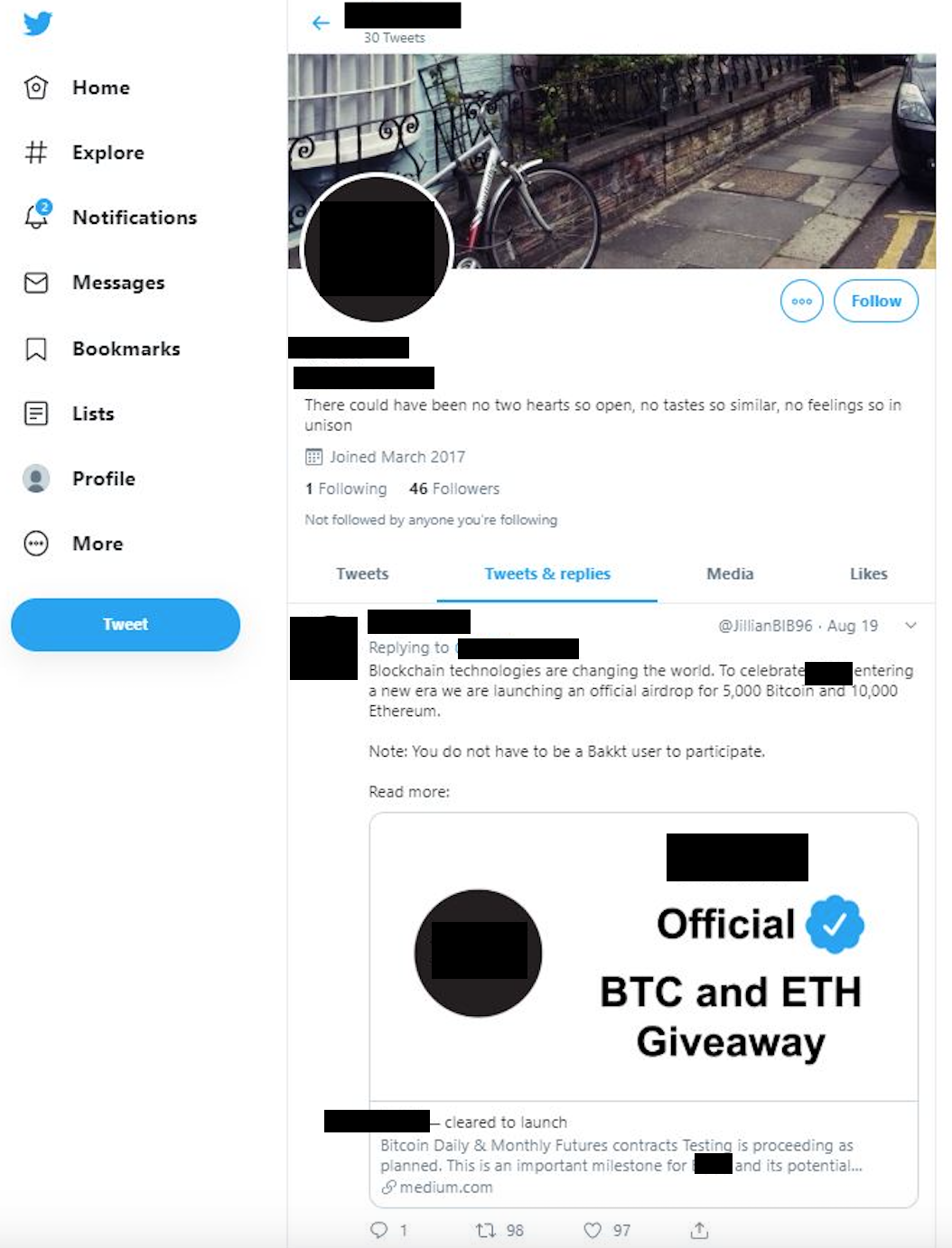
The first example is a fake giveaway on a fraudulent Twitter account. On the page, the unauthorized use of a digital assets platform's logo is displayed multiple times, establishing credibility with the brand. The post promotes a cryptocurrency giveaway where the victim is led to believe they will receive a large amount of Bitcoin or Ethereum if they first submit a small payment of their own.
If the victim communicates with the threat actor through direct message and participates in the scam by transferring money to a digital wallet, they will most likely have no way of getting their stolen funds returned.
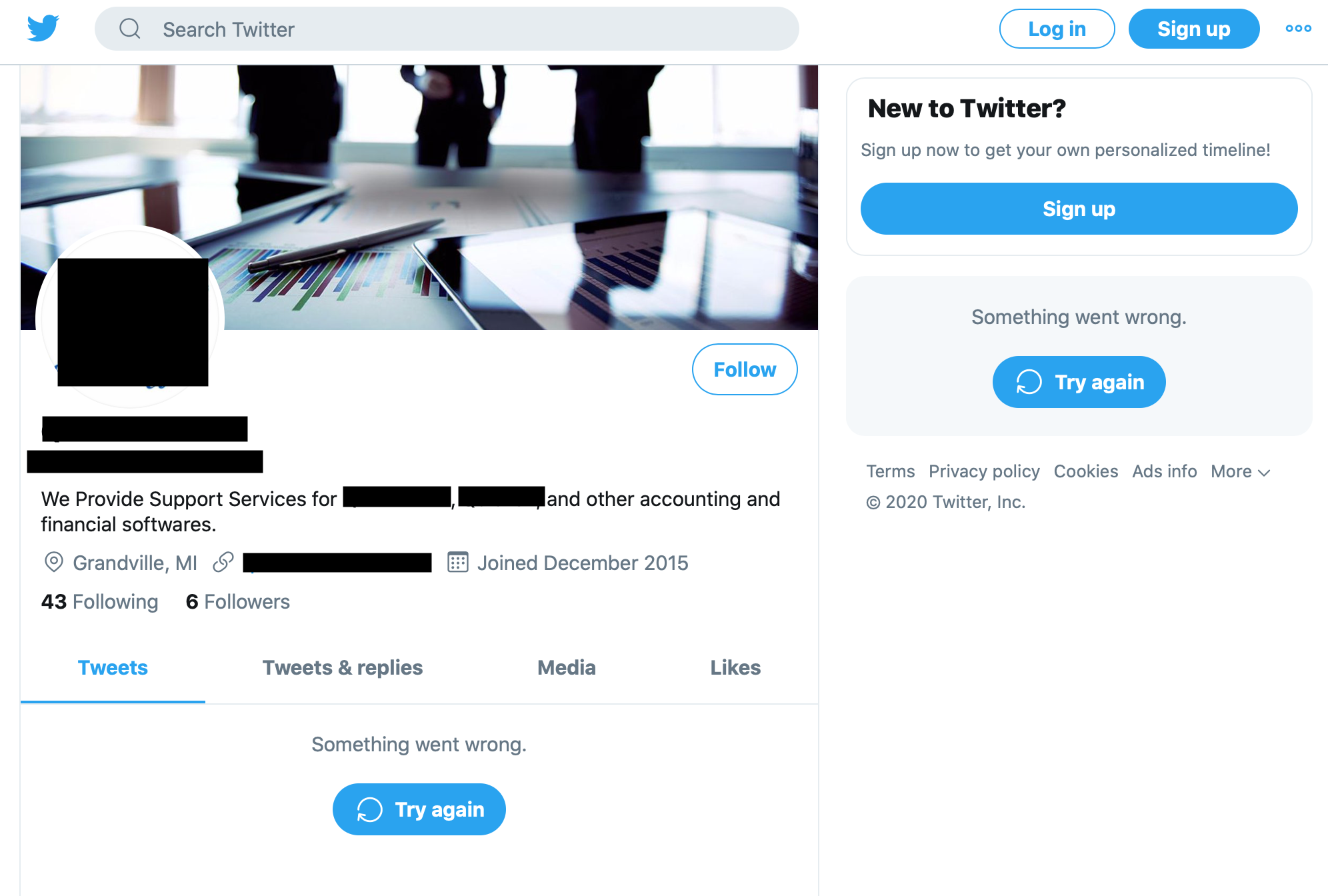
The second example spoofs the support team for a financial and tax preparation software company. This particular organization is often represented by legitimate third-party accounts selling their services online, however in this case, the images and link on this page are unauthorized.
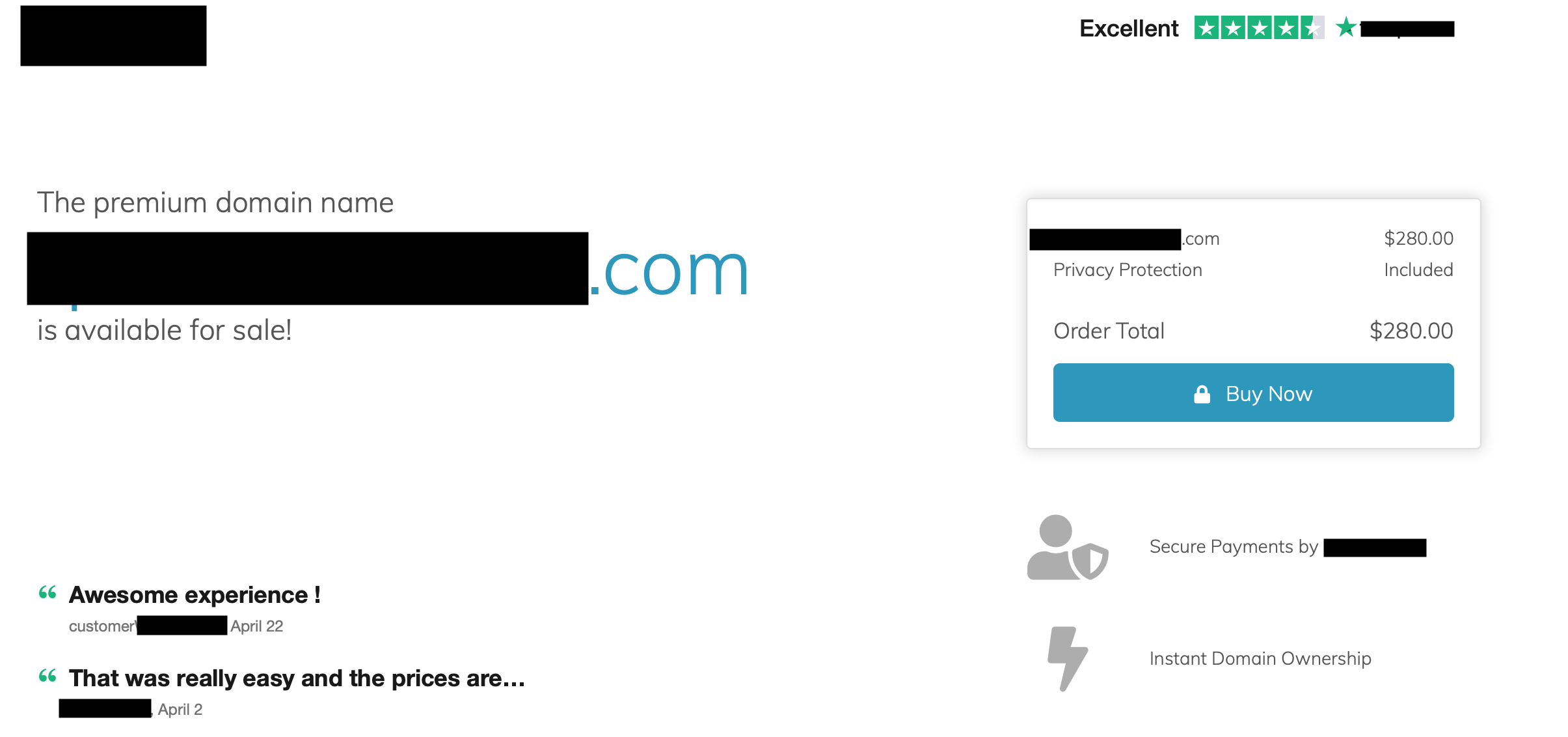
If the victim follows the URL provided, they are led to a page advertising the sale of the very domain represented. If the victim clicks “Buy Now" they are redirected to the Registrar's page where they can indeed purchase it, proving that the domain is not actually active and the Twitter account to be malicious.
Brand impersonation on social media can be harmless or, as the examples above show, lay the foundation for malicious purposes. As society increasingly interacts with businesses and purchases their goods and services online, monitoring for threats related to your organization on popular platforms, as well as the ability to mitigate them, can be the determining factor of its longevity and success.
