
On August 30, Twitter CEO Jack Dorsey became the most notable victim of one of the fastest-growing cyber threats: SIM Swapping. SIM Swap Attacks are increasing because they only require social engineering and access to a SIM card, which makes it another form of phishing.
You can find our definition of phishing here. In a few words, it isn't that difficult.
What is SIM Swapping?
SIM swapping is a malicious technique where threat actors target mobile carriers in an attempt to take over users' bank accounts. The end goal of the attack allows the threat actor to thwart SMS-based two-factor authentication and what it is designed to protect.
This is done in three ways:
- You can payoff an insider at a mobile carrier to port the number
- You can hack the provisioning system (via phishing or other tactic)
- You can impersonate the phone number owner and trick the mobile carrier to port the number
Up until recently, few statistics on successful 2FA attacks have been available as they are rare. However, phishers today are changing that, and by using a combination of old-school techniques and social engineering, they can now convince mobile carriers that they are you, and successfully gain unlimited access to your sensitive information.
Though still uncommon, mobile phone customers in the U.S. and Canada are the prime targets of these attacks and their private accounts such as their banking information is the end goal.
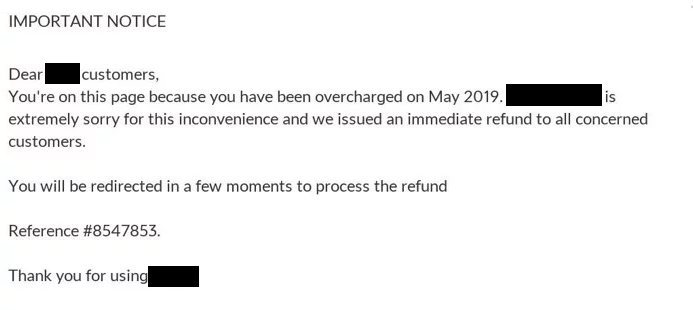
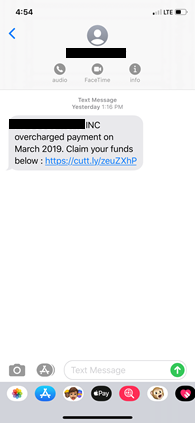
A common attack scenario works as follows: first, a victim receives a phishing lure using brand impersonation to masquerade as an SMS message from their mobile carrier. These typically say something along the lines of “a refund is being issued for a previous overcharge" aka we, owe you money. If the receiver fails to pause and contact their provider through an out-of-band method, the link that they click within the message will prompt them to enter their personal and banking information. This is instantly recorded and sent directly to the threat actor. Also, by clicking on the phishing link, the receiver has confirmed that the cell phone number is an active line.
Now, with stolen information in hand, the threat actor has the ability to search online, confirm the provider of the cell phone user, and call the carrier. All they have to do is answer a few questions using their victim's personal data, convince the cell phone carrier that they are indeed the user, and have the phone number remotely switched to a SIM card which, happens to belong to the scammer.
According to a recent Princeton study, researchers made around 50 attempts across five North American prepaid telecom companies to see if they could successfully port a stolen number (their own) to a SIM card. The end result highlighted weaknesses across each, noting that in most cases a threat actor only needs to answer one question right when questioned by their customer service representative in order reset the password on the account and port the number over.
Now in control of the mobile number, the threat actor can thwart SMS-based 2FA checks that were supposed to protect the user's online bank account. By resetting any of the passwords of the compromised accounts, the full takeover is complete.
One particularly nasty first-hand encounter with a SIM swap attack resulted in the victim having their Coinbase account emptied, which was worth around $100,000 in cryptocurrency.
Example of the initial branded page:
How to Handle Mobile Threats
Threat actors continue to leverage mobile text communication to target victims. PhishLabs' Digital Risk Protection uses threat intelligence as a result of partnerships with mobile carriers to detect and mitigate threats sent via SMS. When active threats are found, PhishLabs analyzes them and identifies victims via phishing credential drops (i.e. files containing all the stolen information). When recovered, the victim's information and compromised credentials are shared with the affected organization and the phishing site is taken offline.
Prevention Methods
Targeted organizations can reduce the threat of attacks by using 2FA methods that can't be exploited remotely. Unlike phone number-based 2FA, Authentication App or device-based 2FA requires the user to have physical possession of the token and help remove the risk of mobile carriers falling for phishers whose social engineering skills are on point.
Mobile carriers also can reduce SIM swap attacks by requiring extra authentication layers such as PINs for remote services.
Additional Resources:
