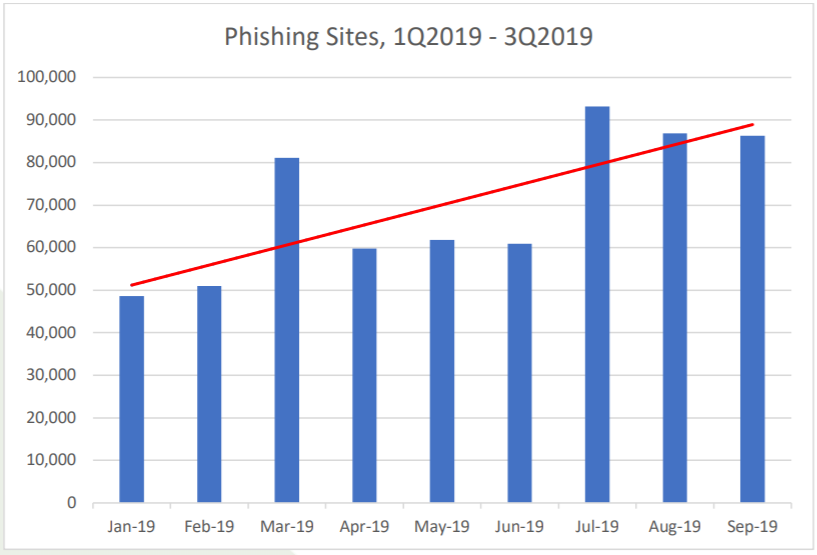
Ransomware continues to be one of the most impactful threats to enterprises. Aside from external vulnerabilities, its primary delivery method remains email phishing, with links or attachments containing early stage loaders. These loaders initiate attacks by compromising systems and installing additional malware. PhishLabs has analyzed these early stage loaders and observed a dramatic increase in ransomware droppers delivered via email. Below are the findings.
Notable Families
PhishLabs studied malware delivered to end users from May 2019 to December 2020. While the second half of 2019 remained stable, reports steadily climbed throughout 2020. Significant observations include a 600% increase in payload delivery between December 2019 and January 2020 as well as a substantial peak during Q3 of 2020.
The most common malware families include:
- Emotet
- Trickbot
- ZLoader
- IceID
- Ursnif/Gozi
- Dridex
- BazarLoader
- QakBot
- Nanocore
- GuLoader
Topping the list of most frequently seen loaders are Emotet, Trickbot, and ZLoader. These banking trojans spread via email campaigns, and traditionally use webinjects to harvest data in compromised systems. All three malware strains have evolved over time and today they commonly act as initial or secondary stage droppers to deliver malware in multistage ransomware attacks. Ryuk, Conti, and Egregor ransomware strains are often associated with these families.
Emotet
Emotet is mostly absent May 2019 through October 2019 before seen in a high volume of phishing attacks throughout the remainder of the study. In Q3 in particular it is the primary malware variant when payloads as a whole exhibited a 300% increase. Ultimately, it is present in 30% of known malware attacks during the study, making it the most observed variant.
Emotet was first seen in 2014 and remains one of the most widely distributed banking trojans. Originally designed to steal credentials, we can attribute its increased use to its evolution to function mainly as a dropper for additional payloads in ransomware attacks.
Emotet's popularity can also be attributed to its availability to threat actors via Malware-as-a-Service (MaaS) where its access to infected systems is sold to the highest bidder. Trickbot, present in almost 25% of the loaders we observed over this same time period, is also used as a MaaS.
Why it Matters
The growing presence of loaders points to increased and continued popularity in ransomware as well as the ongoing threat malicious emails hold to enterprises. Ransomware is rarely delivered first in the attack chain, and the steadily growing observation of these early stage loaders in conjunction with the rise in ransomware attacks confirm that operators are in fact using payloads to set the stage for future assaults.
Learn about how PhishLabs helps organizations defend against ransomware risks with Ransomware Protection.
Additional Resources:
