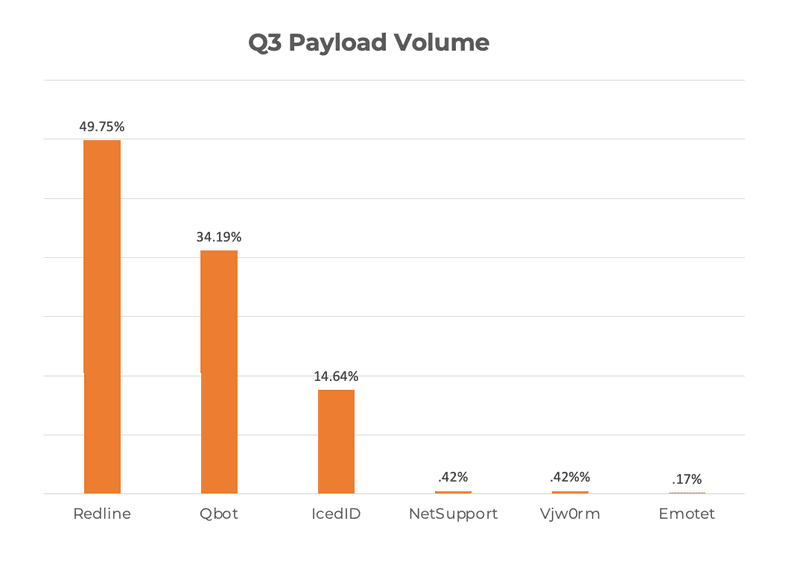
In Q3, Redline Stealer represented nearly half of all malware attacks targeting corporate user inboxes. This is the first quarter Redline has led payload volume since PhishLabs began reporting on malware activity.
Email payloads remain the primary delivery method of ransomware targeting organizations. PhishLabs continuously monitors payload families reported in corporate inboxes to help mitigate attacks targeting their businesses. Below are the top payload threats to enterprises in Q3.
Redline Stealer
In Q3, Redline Stealer was the top reported payload, representing 49.75% of all attacks. Despite emerging in 2020, this is the first quarter Redline was among the top reported payloads by volume.
Redline is a low-cost information stealer capable of grabbing login credentials, processor details, and banking information from compromised machines. The payload is a widely-distributed malware-as-a-service (MaaS), and a large provider of stolen credentials on underground markets. Redline is also self-propagating and capable of downloading and running third party programs on infected devices.
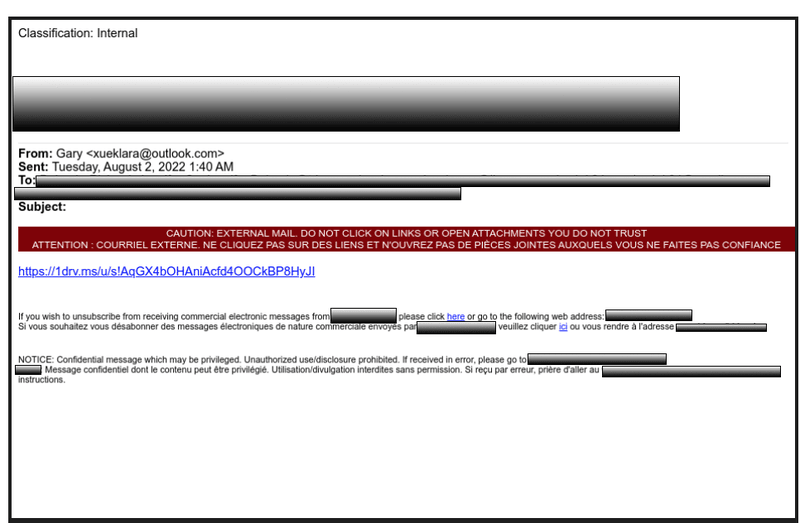
Below is an example of a phishing lure containing a link which drops the Redline payload.
QBot
QBot, also known as Qakbot, was the second most reported payload in Q3, contributing to 34.19% of attacks. QBot is consistently a favorite among criminals and has either ranked first or second among malware varieties for the past four quarters.
QBot is a self-spreading banking trojan known for harvesting credentials, financial information, and more. The payload is also used as a backdoor for additional malicious software and has been connected with Black Basta and Egregor ransomware families. Recent campaigns are being distributed via HTML smuggling, an evasion tactic that hides the payload inside a seemingly benign HTML file.
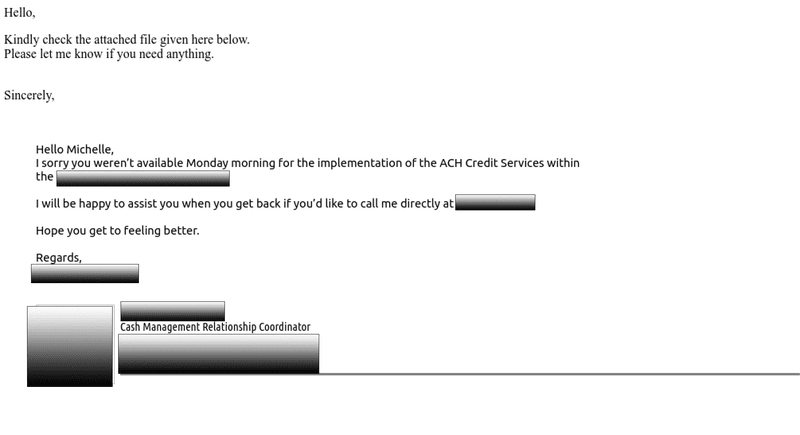
The example below is a phishing lure delivering QBot via HTML attachment. The threat actor used thread hijacking to send the email, enhancing the perceived legitimacy of the message. Thread hijacking is a tactic where malicious messages and malware are incorporated into previously legitimate email threads.
IcedID
IcedID contributed to just under 15% of payload volume in Q3, making it the third most reported malware family in corporate inboxes. First detected in 2017, IcedID is a modular banking trojan known to act as an initial infection vector for ransomware groups such as Conti and Quantum Locker.
IcedID is capable of gathering processor information, stealing financial data, and harvesting credentials. Its authors are consistently updating the payload’s functionality to enhance deliverability and evade detection.
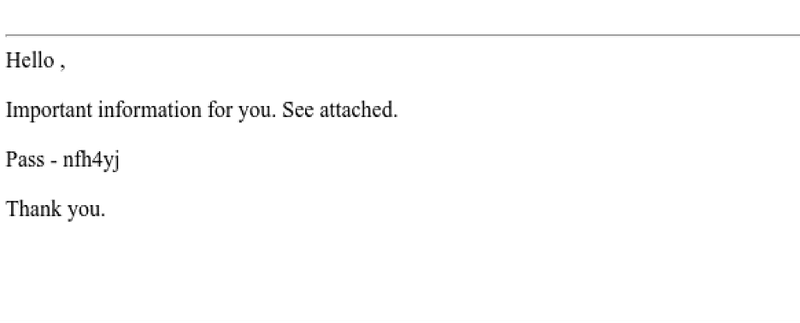
Below is an email lure that contains a password protected IcedID attachment.
Phishing emails containing malicious payloads are a top threat to corporate inboxes, often leading to data loss and damaging ransomware attacks. Payload functionality and delivery tactics are continuously modified, and security teams should prioritize familiarizing themselves with the changing landscape in order to accurately detect threats. PhishLabs continuously monitors for malicious email activity to protect organizations from damaging malware attacks.
