
In order to increase the lifespan of their campaigns, most threat actors implement evasion techniques to keep their activity from being detected by defenders and their intelligence tools. In this blog post, we'll take a look at how geoblocking by IP is used.
Geoblocking by IP takes advantage of the victim's location. It is often used on sites hosting malicious content to limit the exposure of the malicious content to visitors from a target geographic area. If the visitor is in the wrong geographical region, they will see benign content instead. This can include fake down pages (e.g. 404 not found, 403 unauthorized, account suspended, etc.), the legitimate website of the brand being abused, advertising sites, adult sites, or even just a blank white screen.
This poses a challenge for automated crawling tools used by defenders to efficiently scan sites for malicious content. If the crawling is performed from outside the targeted area, no malicious content will be served and the attack will remain undetected. Detecting sites using geoblocking and other evasion techniques requires a combination of technology and expertise that can recognize these behaviors and trigger deeper investigation to uncover hidden content.
Below is an example of a webpage we encountered while investigating an attack targeting a Canadian company. When attempting to access the malicious URL from the United States, we were directed to this Account Suspended page. At first glance, it looked as though the hosting provider had already taken this attack offline. However, when attempting to access the same attack while simulating a Canadian location, the website resolved and revealed that the offline page was fake.
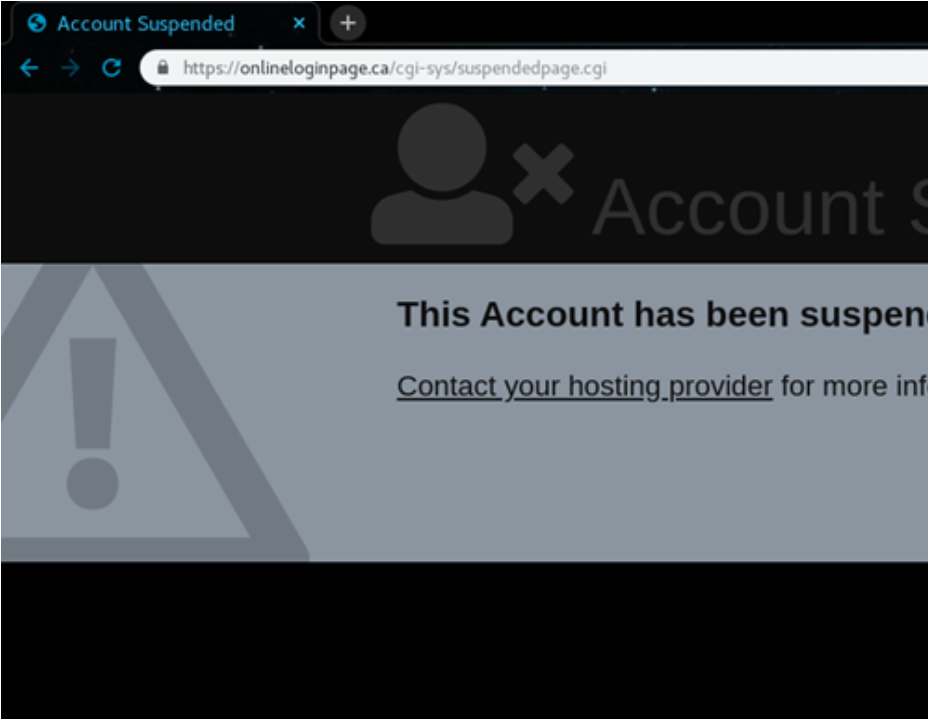
What non-targets see when accessing the malicious URL.

What the target is intended to see.
Getting Around Geoblocking
When a threat actor attempts to lock in their malicious sites by region, those outside of the target area have a few options. These all involve changing connection settings within the user's computer so that it appears to come from somewhere other than its physical location. It is, of course, necessary to know the intended target region first, otherwise each attempt to access is a shot in the dark.
The most common approach is to use a VPN or a proxy that routes the users traffic through servers with IP addresses associated with a specified region. VPNs have the added benefit of encrypting all user traffic, so they are a go-to option for those concerned with privacy. Most security professionals already have access to some form of VPN or proxy, which allows them to simply select the area targeted by an attack and make their computer look like a potential victim.
Another method for circumventing geoblocking is onion routing, the most common form of which can be found in the Tor network. This process is best expressed by The Tor Project themselves:
“The goal of onion routing was to have a way to use the internet with as much privacy as possible, and the idea was to route traffic through multiple servers and encrypt it each step of the way."
This approach is so effective at masking a user's actual identity (including location) that it is often used by criminals to access the dark web, where they can safely engage in illicit activity. Security professionals; however, use the Tor network to protect themselves as they access dangerous content, including phishing websites.
Additionally, some services such as SmartDNS offer DNS spoofing. This is another way to make a user appear to come from a certain region. This approach has the advantage of speed, as it only attempts to spoof DNS requests. But it is not used as commonly as VPNs or conventional proxies, as it does not spoof the user's IP, and it does not encrypt any traffic.
Why Threat Actors Use Blocking Techniques
At first glance, it can seem counter intuitive for an attacker to limit the scope of an attack. From the perspective of the threat actor, we might suppose that the more opportunities to steal credentials, the better. However, if we approach phishing as a business venture, an investment with costs and potential benefits, limiting the scope and blocking access makes sense.
For starters, there is always a cost involved with setting up an attack campaign. This can be minimal, with certain sites offering to host content for free; all the attacker needs is to invest either a small amount of time setting up their malicious content or spend money on a kit containing the everything they need.
At times, though, an attacker may choose to spend a few hundred dollars for a look-a-like domain, hosting with greater availability, and a complex kit with multiple layers of input validation and baked-in blocking techniques. This greater cost is justified by the prospect of a greater return, and PhishLabs often sees these attacks targeting a small set of highly-lucrative targets. By limiting an attack to such a small surface, a threat actor can ensure that the vast majority of a malicious site's views come from bonafide targets.
In either case, whether the investment is small or large, it is in the threat actor's best interest that the attack remains active long enough to provide a return on this investment. And if only those targeted by the attack are able to access it, this makes it much more difficult for security professionals to detect and report it to the responsible organizations.
Additional Resources:
