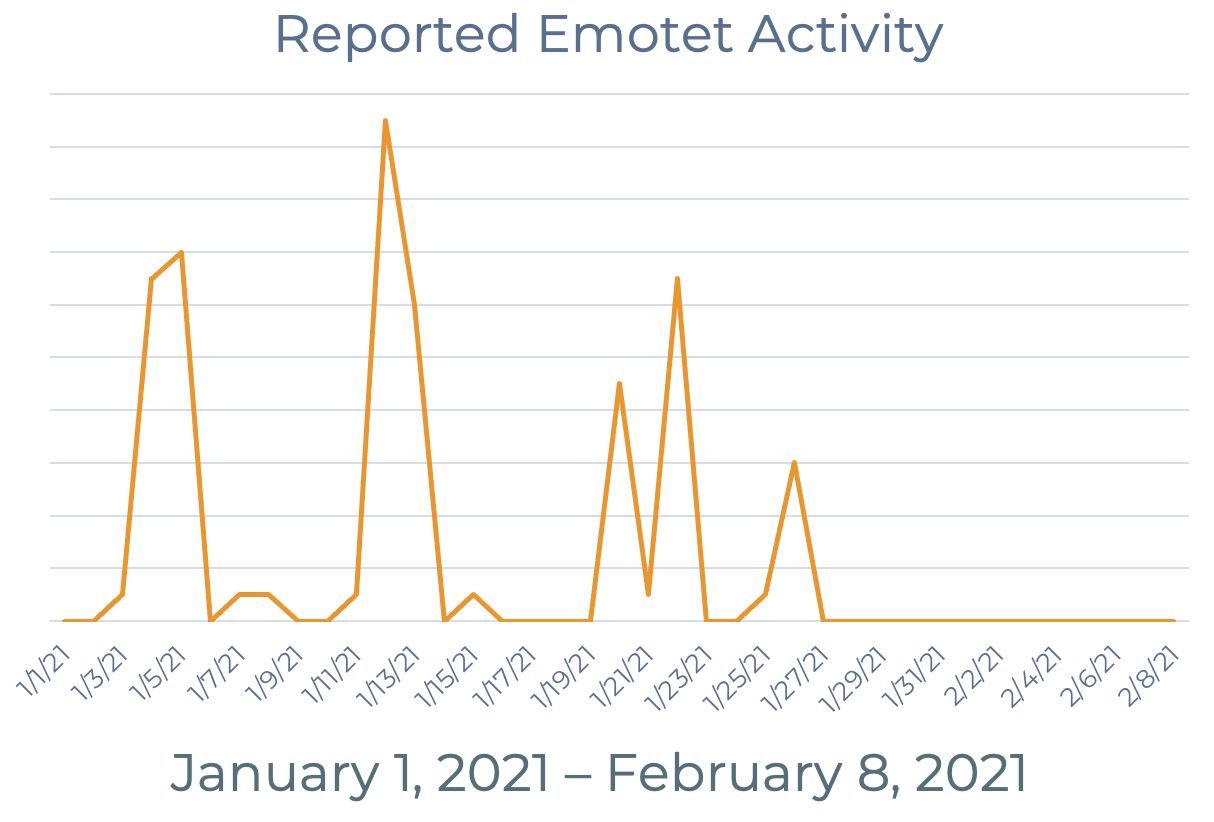
Recently, we published a piece highlighting early stage loaders often used in ransomware attacks. One of the most prolific was Emotet, which has since been taken down via a coordinated, multi-national effort. How will this impact the threat landscape? In this post, we take a look at loader activity in the aftermath of the Emotet takedown.
Predominant Payloads
In 2020, Emotet, Trickbot, and ZLoader were the loaders of choice for actors, contributing to 78% of the overall loader volume.
In 2021, we continue to see reports of Trickbot and ZLoader, as well as the dropper BazarLoader (often associated with Trickbot campaigns). BazarLoader was mostly absent during 2020, with activity first reported in Q4 of 2020. Emotet has been silent since operations were taken over January 26.
If Emotet remains inactive, we expect to see attention turn to other Malware-as-a-Service competitors. In January 2021, Trickbot proved the most dominant, active loader alongside Emotet, representing 22% of all malware reported. In 2020, Trickbot operators took full advantage of the pandemic, first delivering an onslaught of attacks in April as businesses were shifting to remote work. Their numbers peaked again in September as Trickbot targeted vulnerable healthcare systems, so much so that the FBI issued an increased and imminent threat warning.
In an attack reminiscent of Emotet's recent takedown, Trickbot was partially disrupted in a joint effort by cyber command and Microsoft in October. It has since bounced back. Trickbot is most often linked with the Ryuk and Conti ransomware variants.
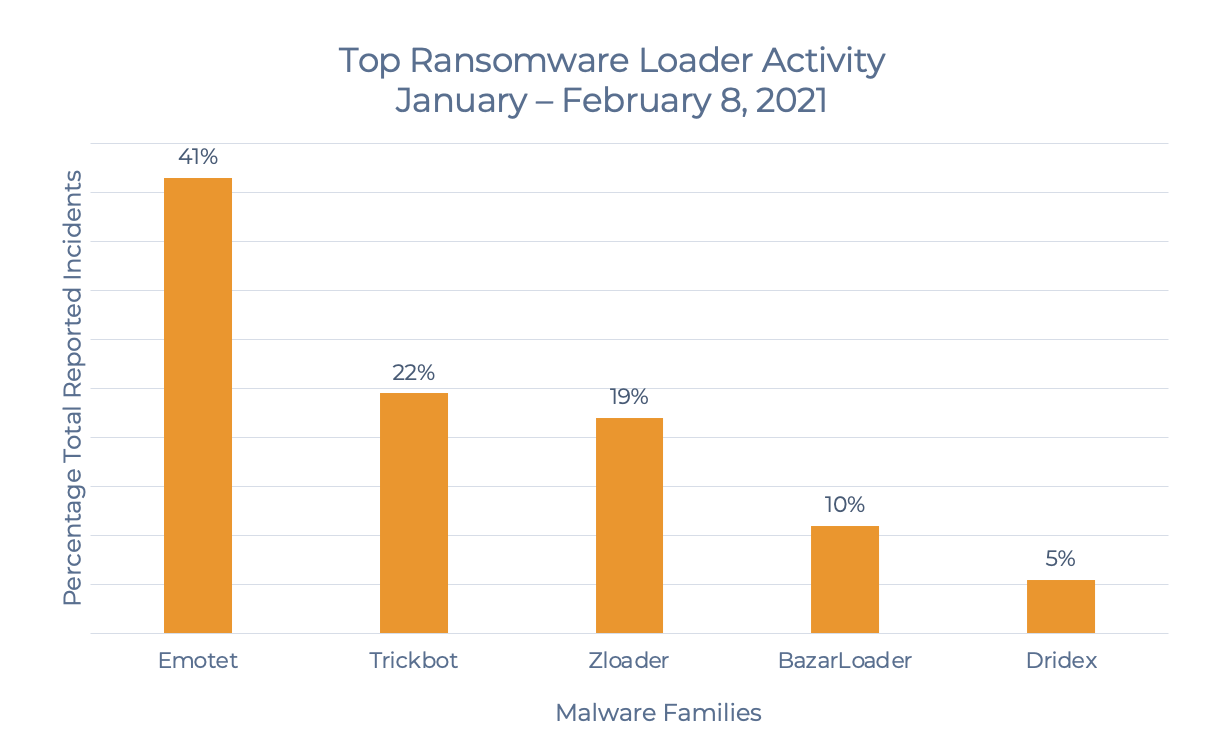
ZLoader was absent May 2019 - April 2020, however operators made up for lost time with an aggressive presence through the remainder of the year. In January 2021, we saw a slight dip in reports of ZLoader before a significant increase so far in February. ZLoader accounts for 19% of all malware reported January - February 8, 2021.
ZLoader is a variant of the Zeus family that is known for installing Zeus-based malware onto infected systems. It is distributed through phishing emails and has strong connections to Ryuk and Egregor ransomware.
Often working in tandem with Trickbot, BazarLoader is starting off the new year strong, representing 10% of all malware activity. If numbers continue to increase, it may be an indicator that former Emotet operators are incorporating BazarLoader into their campaigns. BazarLoader is an entry point for the Ryuk ransomware.
Like Emotet, Trickbot and ZLoader's popularity may be fueled by their roles as MaaS, giving threat actors of all experience levels easy access to infected systems where they can distribute additional malware and conduct ransomware attacks.
As 2020 came to a close, email phishing overtook RDP as the top vector for ransomware attacks. With Emotet operators out of the cybercrime business, it remains to be seen whether phishing will continue to trend upward or if actors will instead opt to return to brute force attacks. With other malware variants emerging and MaaS giving inexperienced criminals the opportunity to execute campaigns, threat actors have multiple options available to advance their attacks.
Learn about how PhishLabs helps organizations defend against ransomware risks with Ransomware Protection.
Additional Resources:
