We continue to see a wide range of lures exploiting coronavirus fears. In this post, we take a look at three recently observed lure samples that use the possibility of a cure to entice victims.
We are providing ongoing updates on coronavirus-themed attacks observed by the PhishLabs team. This post and others are meant to help the security community stay up-to-date on how threat actors are exploiting the pandemic.
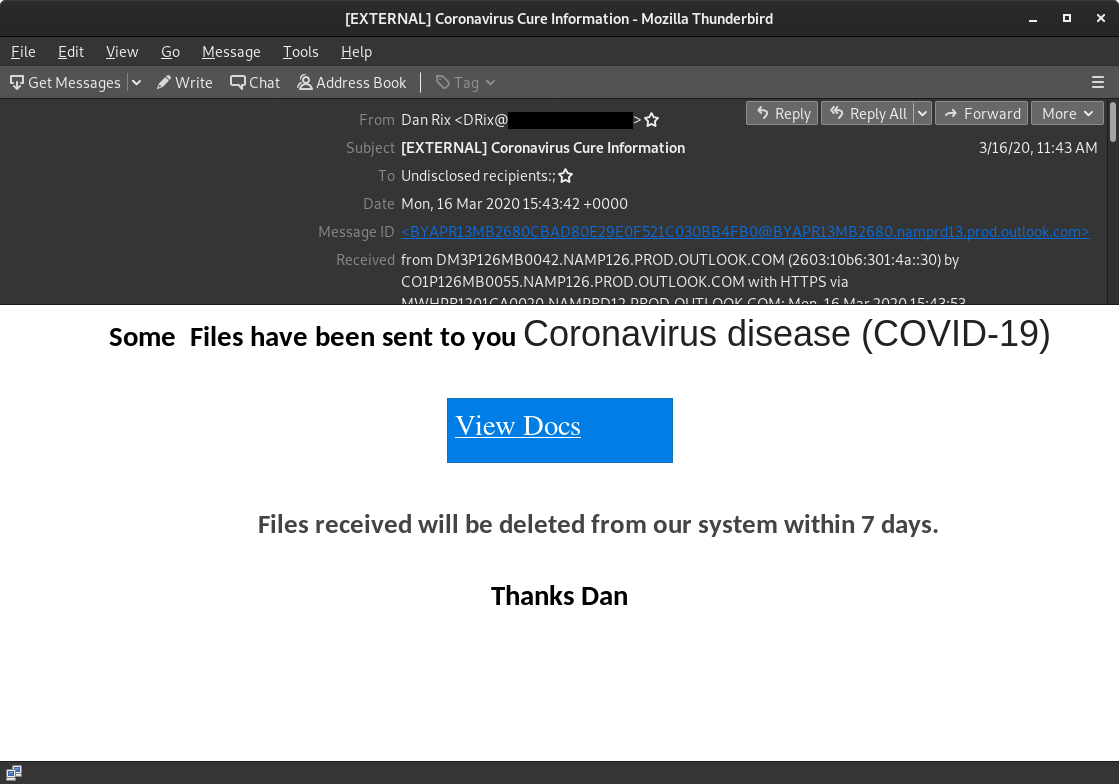
The first example is a targeted phish that leads to a malicious site in order to steal Microsoft Office 365 credentials. The sender's address is spoofed and the message itself urges the victim to click on time stamped files in order to access information on a cure.
Actual sender IP: 67.231.149.113
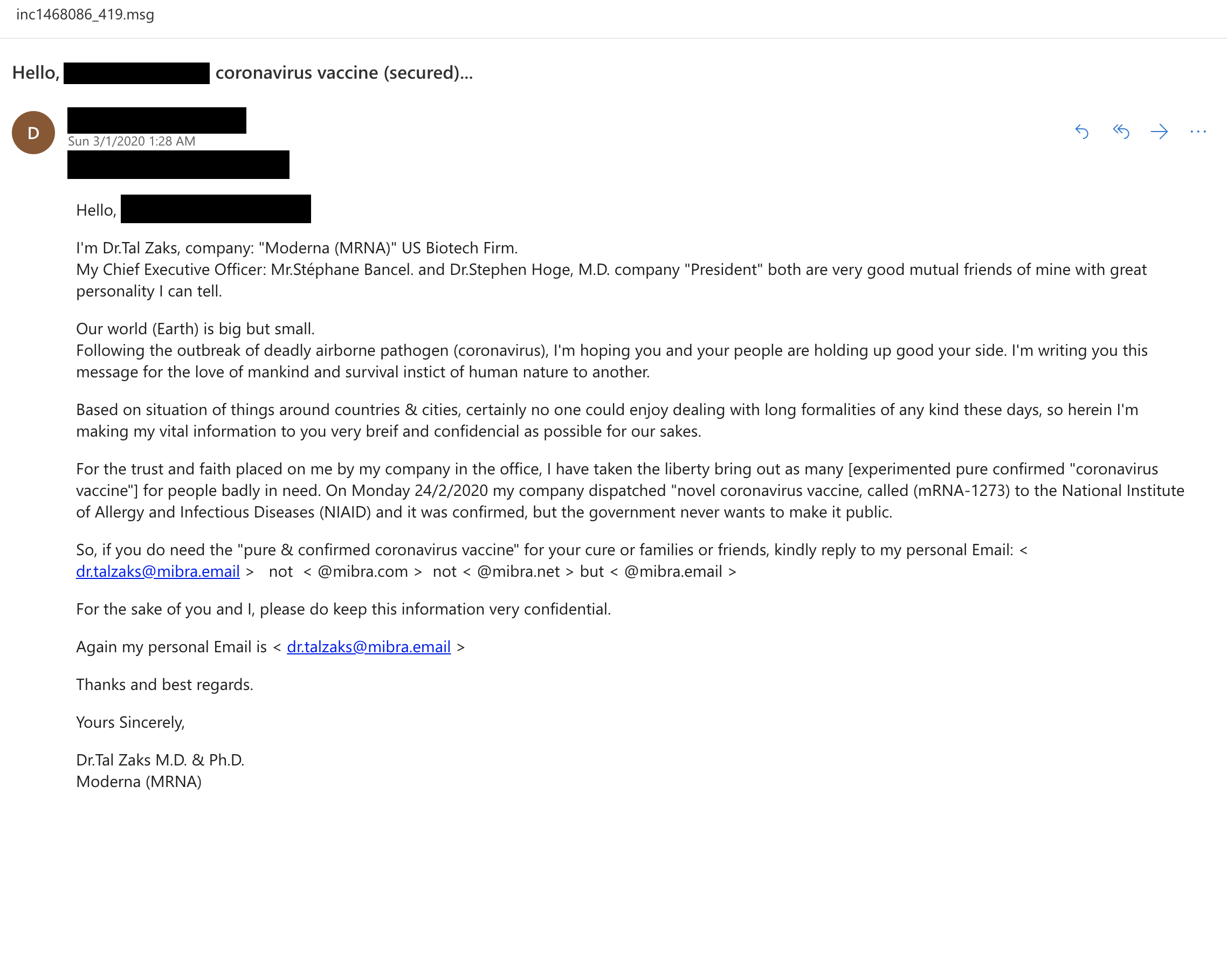
The second email claims to be from a U.S. biotech firm secretly bypassing the National Institute of Allergy and Infectious Diseases (NIAID) in order to give you information on the COVID-19 vaccine. This lure encourages the victim to reply to the email address listed in the body. The motive is unknown without playing along, but this type of lure traditionally is looking for money or PII.
Sender: [email protected]
Registrant [email protected] just registered shrespects.com 2020-01-15 in Lagos Nigeria.
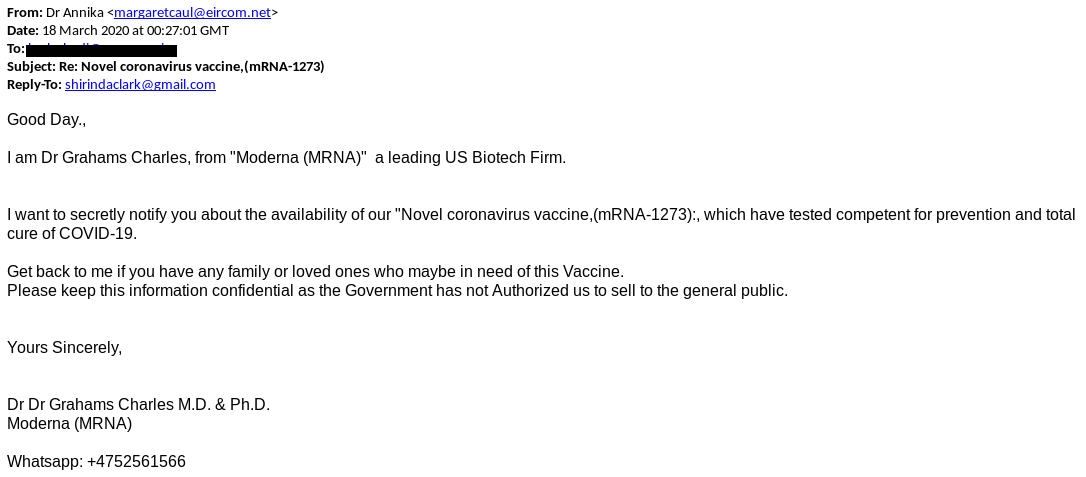
The third lure is similar to the second, being that we cannot be certain of the motive without interacting with the scammer. Note that the sender's name does not match the email, nor the reply-to.
Sender: Dr Annika [email protected]>
Reply-to: [email protected]
WHO is actively working to repurpose vaccines to slow or stop the pandemic, and threat actors know this. With social media saturated with information that is ever-changing around the development of a potential cure, cybercriminals have a unique opportunity to masquerade as authority figures communicating critical information - a tactic not formerly utilized in past campaigns.
Additional Resources:
