Threat actors are using the novel coronavirus to impersonate accounts on social media. The example below targets members of a credit union.
We are providing ongoing updates on coronavirus-themed attacks observed by the PhishLabs team. This post and others are meant to help the security community stay up-to-date on how threat actors are exploiting the pandemic.
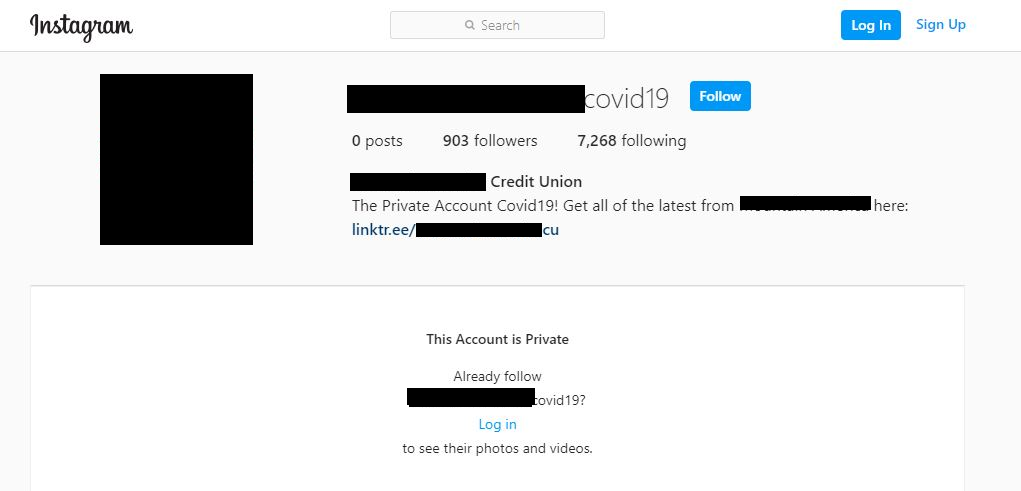
The threat actor created a private Instagram account referencing COVID-19 that used the credit union's name, its logo, and link to its legitimate website.
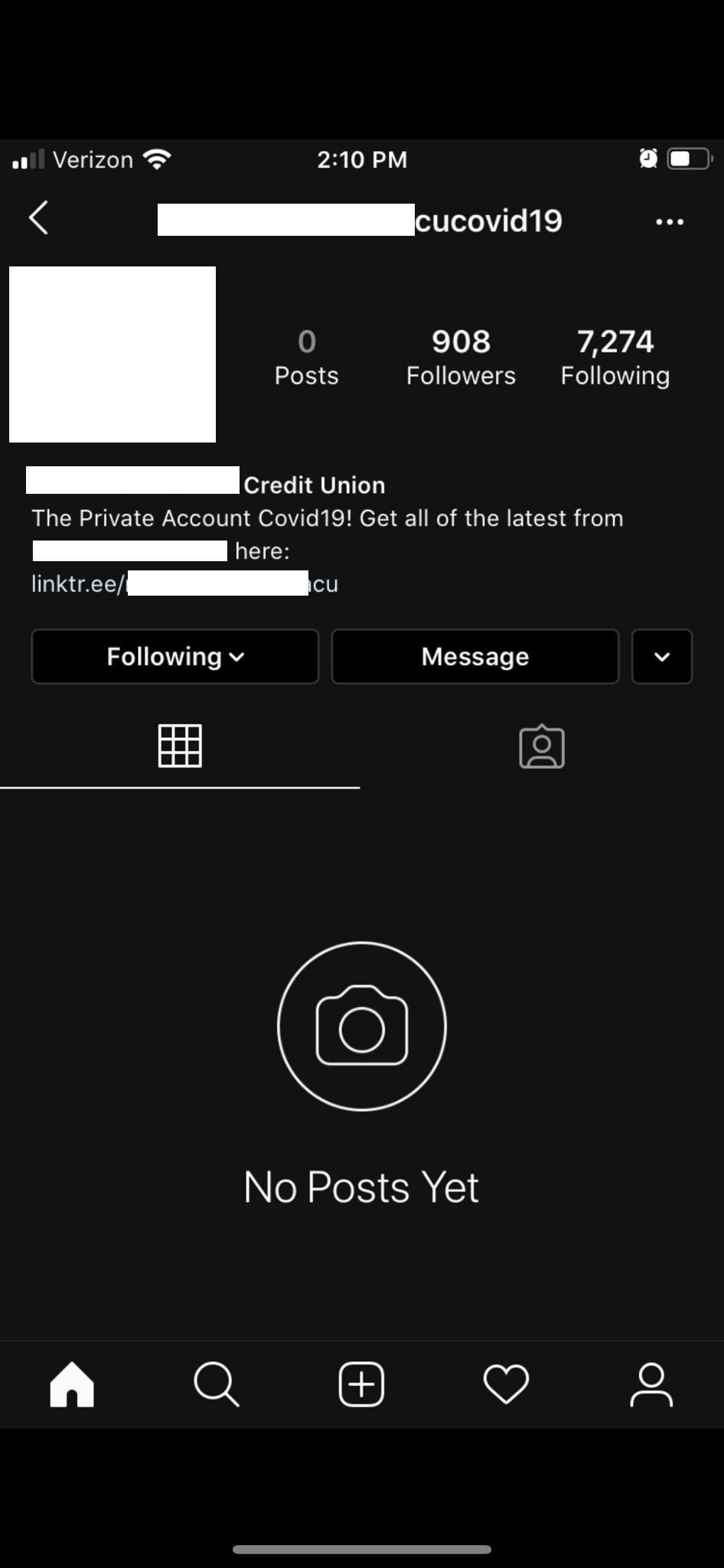
URL: hxxps://www(dot)instagram(dot)com/{redacted}covid19/?igshid=6wj8at1zpwq4
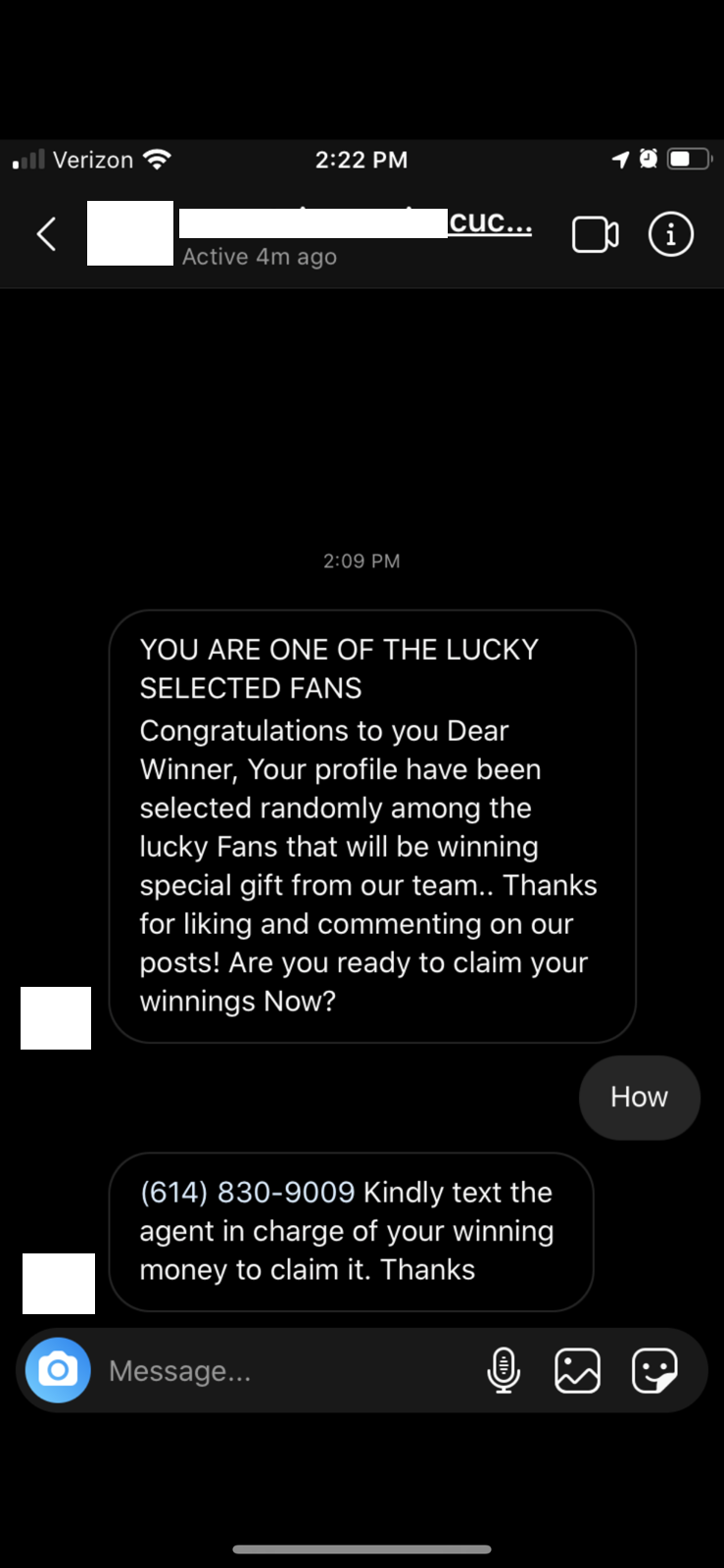
The victim received a direct message from the account claiming their profile had been selected to receive a gift. The cyber criminal then followed up with a phone number.
Once they engaged via text, the threat actor requested the member's account information and password in order to claim their money. If given, the account could be compromised.
As many of us continue to shelter in place, the internet is dominating the way we work and communicate, and opportunistic cyber criminals know that individuals generally skeptical of suspicious emails may be less likely to view social media as a threat vector. Instagram is simply one outlet where they are using COVID-19 to prey on those who aren't vigilant.
For more intelligence on COVID-19 threats, see our ongoing coverage.